CEN-5079: 11.April.2019
1
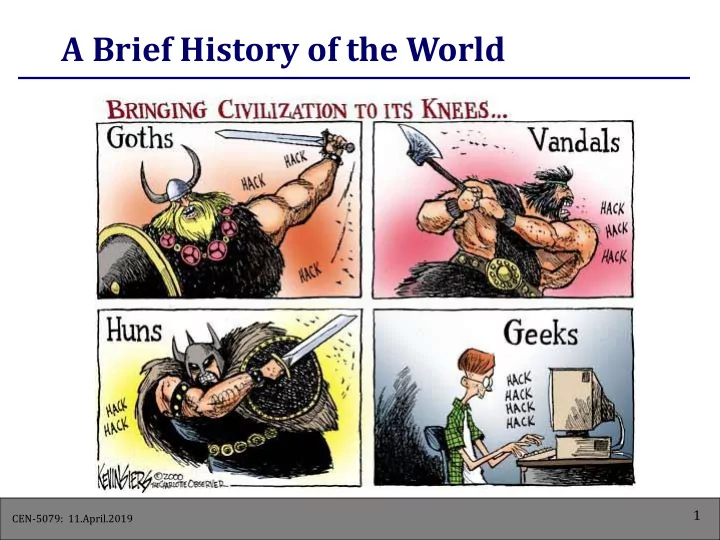
A Brief History of the World 1 CEN-5079: 11.April.2019 Network - - PowerPoint PPT Presentation
A Brief History of the World 1 CEN-5079: 11.April.2019 Network Security Lecture 10 2 CEN-5079: 11.April.2019 Why and Who Attack Networks ? Challenge : Hackers Money : Espionage Money : Organized Crime Ideology :
CEN-5079: 11.April.2019
1
CEN-5079: 11.April.2019
2 Lecture 10
CEN-5079: 11.April.2019
3
CEN-5079: 11.April.2019
4
CEN-5079: 11.April.2019
5
CEN-5079: 11.April.2019
6
CEN-5079: 11.April.2019
7
CEN-5079: 11.April.2019
8
CEN-5079: 11.April.2019
9
CEN-5079: 11.April.2019
10
CEN-5079: 11.April.2019
11
CEN-5079: 11.April.2019
12
CEN-5079: 11.April.2019
13
CEN-5079: 11.April.2019
14
CEN-5079: 11.April.2019
15
CEN-5079: 11.April.2019
16
CEN-5079: 11.April.2019
17
CEN-5079: 11.April.2019
18
CEN-5079: 11.April.2019
19
CEN-5079: 11.April.2019
20
CEN-5079: 11.April.2019
21
CEN-5079: 11.April.2019
22
CEN-5079: 11.April.2019
23
CEN-5079: 11.April.2019
24
CEN-5079: 11.April.2019
25
CEN-5079: 11.April.2019
26
CEN-5079: 11.April.2019
27
CEN-5079: 11.April.2019
28
CEN-5079: 11.April.2019
29
CEN-5079: 11.April.2019
30
CEN-5079: 11.April.2019
31
CEN-5079: 11.April.2019
32
CEN-5079: 11.April.2019
33
CEN-5079: 11.April.2019
34
CEN-5079: 11.April.2019
35
CEN-5079: 11.April.2019
36
CEN-5079: 11.April.2019
37
CEN-5079: 11.April.2019
38
CEN-5079: 11.April.2019
39
CEN-5079: 11.April.2019
40
CEN-5079: 11.April.2019
41
CEN-5079: 11.April.2019
42
CEN-5079: 11.April.2019
43
CEN-5079: 11.April.2019
44
CEN-5079: 11.April.2019
45
CEN-5079: 11.April.2019
46 Internet Perpetrator Victim
ICMP echo (spoofed source address of victim) Sent to IP broadcast address ICMP echo reply
CEN-5079: 11.April.2019
47
CEN-5079: 11.April.2019
48
CEN-5079: 11.April.2019
49
CEN-5079: 11.April.2019
50
CEN-5079: 11.April.2019
51
CEN-5079: 11.April.2019
52
CEN-5079: 11.April.2019
53
CEN-5079: 11.April.2019
54
CEN-5079: 11.April.2019
55
CEN-5079: 11.April.2019
56
CEN-5079: 11.April.2019
57