SLIDE 1
Department of Computer Science - COS 121 September 2012 Christoph Stallmann - University of Pretoria 1 COS 121 – Christoph Stallmann
1
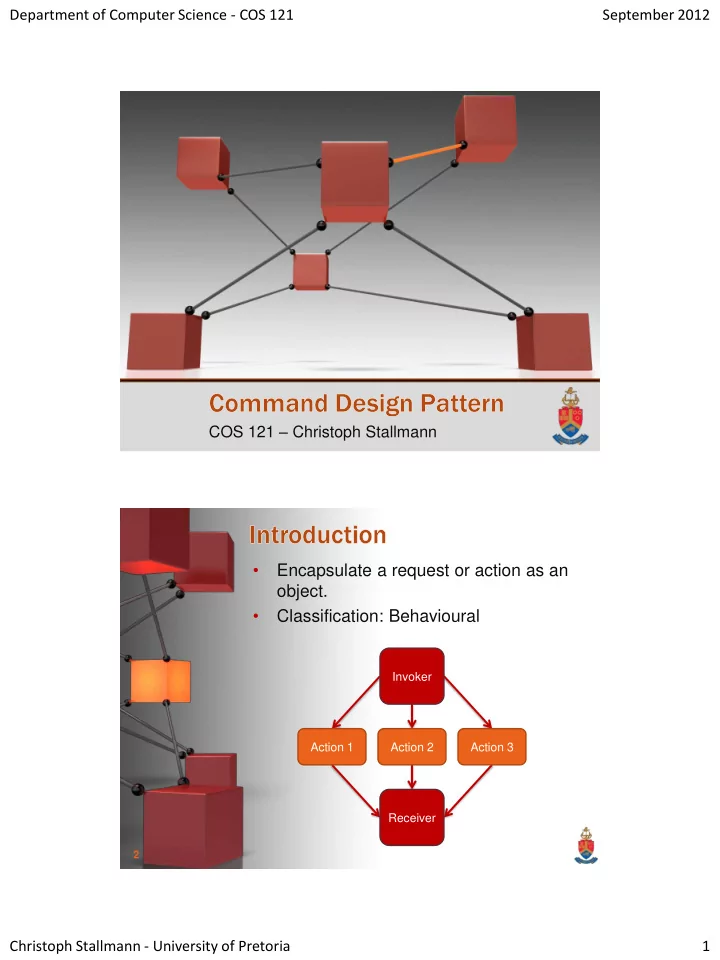
- Encapsulate a request or action as an
- bject.
- Classification: Behavioural