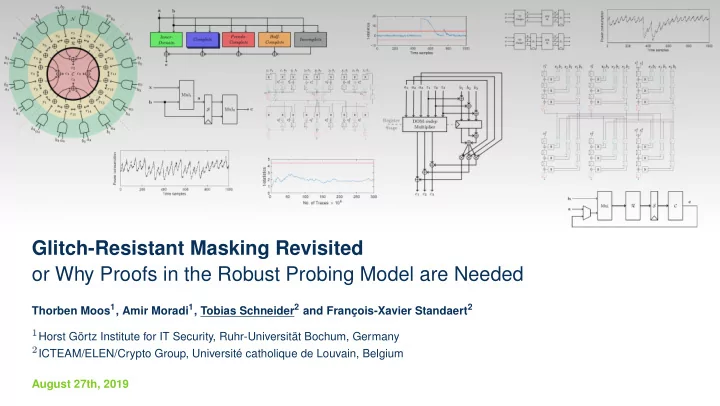
Glitch-Resistant Masking Revisited
- r Why Proofs in the Robust Probing Model are Needed
Thorben Moos1, Amir Moradi1, Tobias Schneider2 and François-Xavier Standaert2
✶Horst Görtz Institute for IT Security, Ruhr-Universität Bochum, Germany ✷ICTEAM/ELEN/Crypto Group, Université catholique de Louvain, Belgium
August 27th, 2019