SLIDE 1
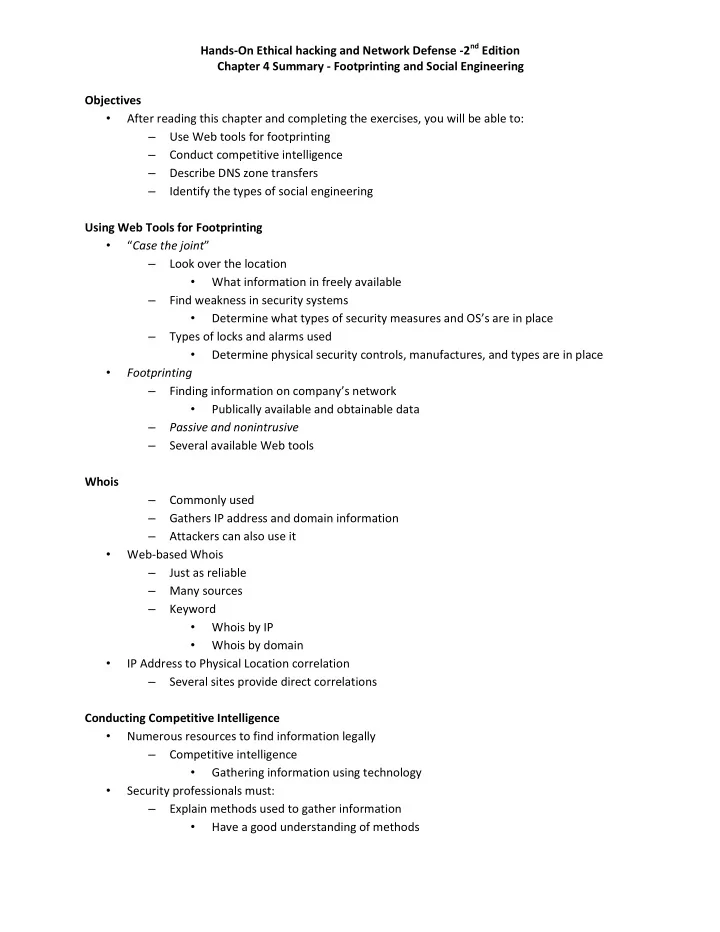
Hands-On Ethical hacking and Network Defense -2nd Edition Chapter 4 Summary - Footprinting and Social Engineering Objectives
- After reading this chapter and completing the exercises, you will be able to:
– Use Web tools for footprinting – Conduct competitive intelligence – Describe DNS zone transfers – Identify the types of social engineering Using Web Tools for Footprinting
- “Case the joint”
– Look over the location
- What information in freely available
– Find weakness in security systems
- Determine what types of security measures and OS’s are in place
– Types of locks and alarms used
- Determine physical security controls, manufactures, and types are in place
- Footprinting
– Finding information on company’s network
- Publically available and obtainable data
– Passive and nonintrusive – Several available Web tools Whois – Commonly used – Gathers IP address and domain information – Attackers can also use it
- Web-based Whois
– Just as reliable – Many sources – Keyword
- Whois by IP
- Whois by domain
- IP Address to Physical Location correlation
– Several sites provide direct correlations Conducting Competitive Intelligence
- Numerous resources to find information legally
– Competitive intelligence
- Gathering information using technology
- Security professionals must:
– Explain methods used to gather information
- Have a good understanding of methods