SLIDE 1
AUTOMATED REASONING SLIDES 16: KNUTH BENDIX COMPLETION Basic steps of Knuth Bendix completion Aspects of Critical Pair Formation Knuth Bendix Procedure Outline of Correctness KB - AR - 2009
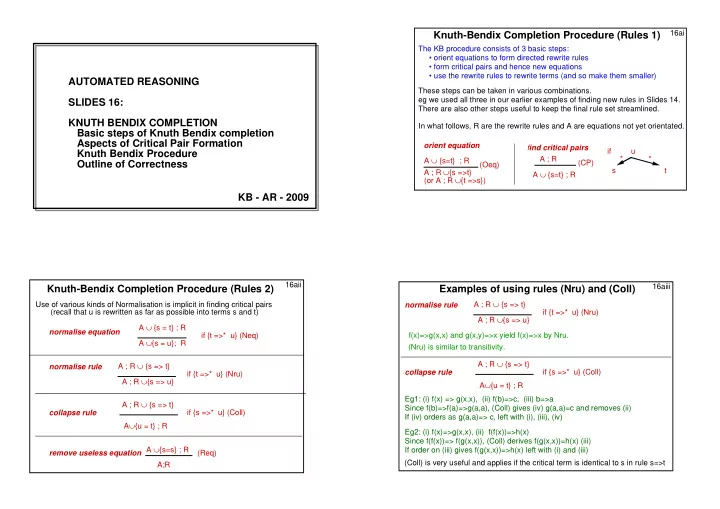
In what follows, R are the rewrite rules and A are equations not yet orientated.
Knuth-Bendix Completion Procedure (Rules 1)
16ai A ∪ {s=t} ; R A ; R ∪{s =>t} (or A ; R ∪{t =>s})
- rient equation
(Oeq) A ; R A ∪ {s=t} ; R find critical pairs if u s t * * (CP) The KB procedure consists of 3 basic steps:
- orient equations to form directed rewrite rules
- form critical pairs and hence new equations
- use the rewrite rules to rewrite terms (and so make them smaller)