Managing Security Investment
Part IV Tyler Moore
Computer Science & Engineering Department, SMU, Dallas, TX
September 27, 2012
Baseline investment models Information security risk management Measuring the security level
Outline
1
Baseline investment models Linear breach probability function Exponential breach probability function Investment models in R
2
Information security risk management Risk acceptance Risk mitigation Risk avoidance
3
Measuring the security level
2 / 27 Baseline investment models Information security risk management Measuring the security level Linear breach probability function Exponential breach probability function Investment models in R
Linear breach probability function
Let’s start with the simplest possible model
1 We use the Bernoulli loss assumption
Two outcomes {0, λ} 0 : 1 − ps, λ : ps
2 We assume security investment is effective
c = λs For unit loss λ = 1: c = s
3 We can even use a linear breach probability function
S(s, v) = v · (1 − s) for s ∈ [0, 1].
4 / 27 Baseline investment models Information security risk management Measuring the security level Linear breach probability function Exponential breach probability function Investment models in R
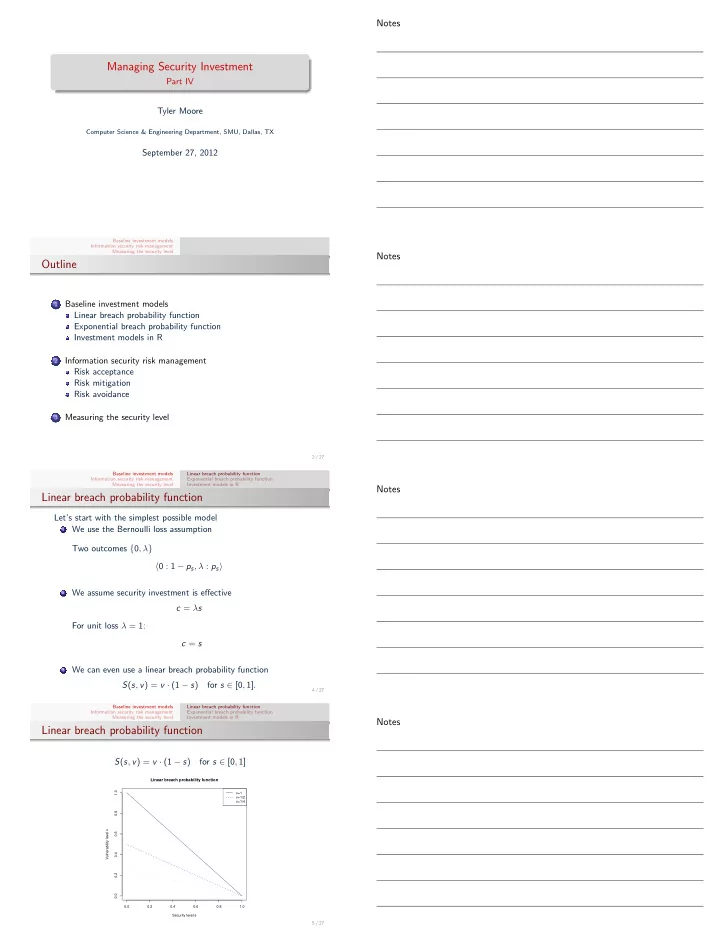
Linear breach probability function
S(s, v) = v · (1 − s) for s ∈ [0, 1]
0.0 0.2 0.4 0.6 0.8 1.0 0.0 0.2 0.4 0.6 0.8 1.0
Linear breach probability function
Security level s Vulnerability level v v=1 v=1/2 v=1/4
5 / 27