Modeling filter configuration
Tyler Moore
Computer Science & Engineering Department, SMU, Dallas, TX
CSE 5/7338 Lecture 9
Optimal filter configuration ROC curves An economic model of optimal filter configuration
Domain-specific models
Up to now we have modeled security investment at a very high level Map costs to benefits, assume diminishing marginal returns to investment, etc. Useful for when justifying security budgets compared to non-security expenditures Not useful for deciding how best to allocate a given security budget Today, we discuss a model for a tactical security investment decision: configuring a filter to balance false positives and negatives
3 / 15 Optimal filter configuration ROC curves An economic model of optimal filter configuration
Binary classification is a recurring problem in CS
Common task: distill many observations to a binary signal
{0, 1}: communications theory S = {undervalued, overvalued}: stock trading S = {reject, accept}: research hypothesis S = {benign, malicious}: security filter
Such simplification inevitably leads to errors compared to reality (aka ground truth)
4 / 15 Optimal filter configuration ROC curves An economic model of optimal filter configuration
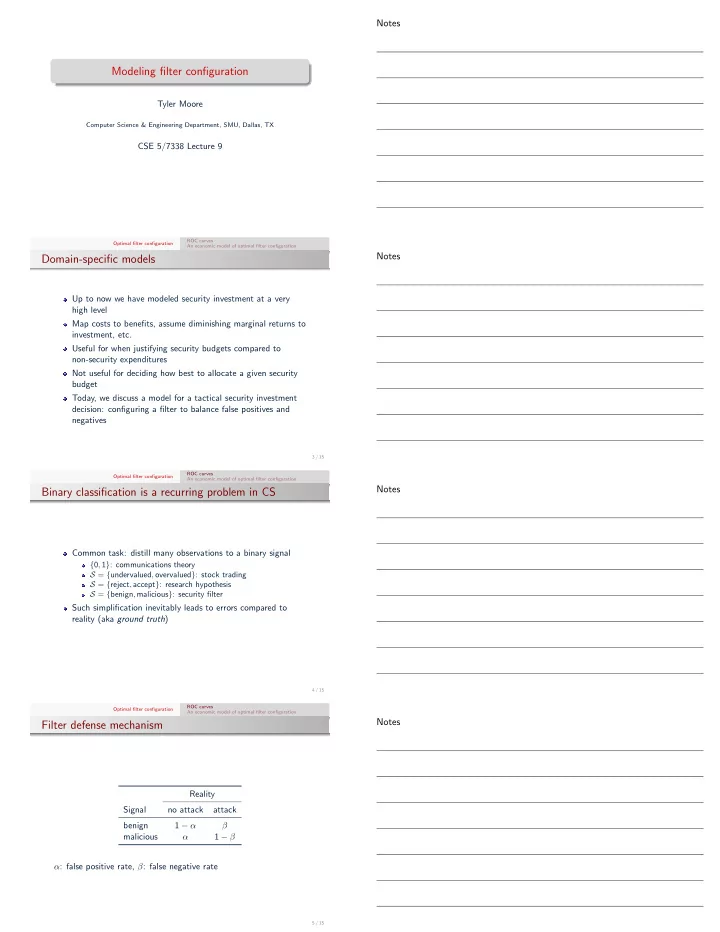
Filter defense mechanism
Reality Signal no attack attack benign 1 − α β malicious α 1 − β α: false positive rate, β: false negative rate
5 / 15