SLIDE 1
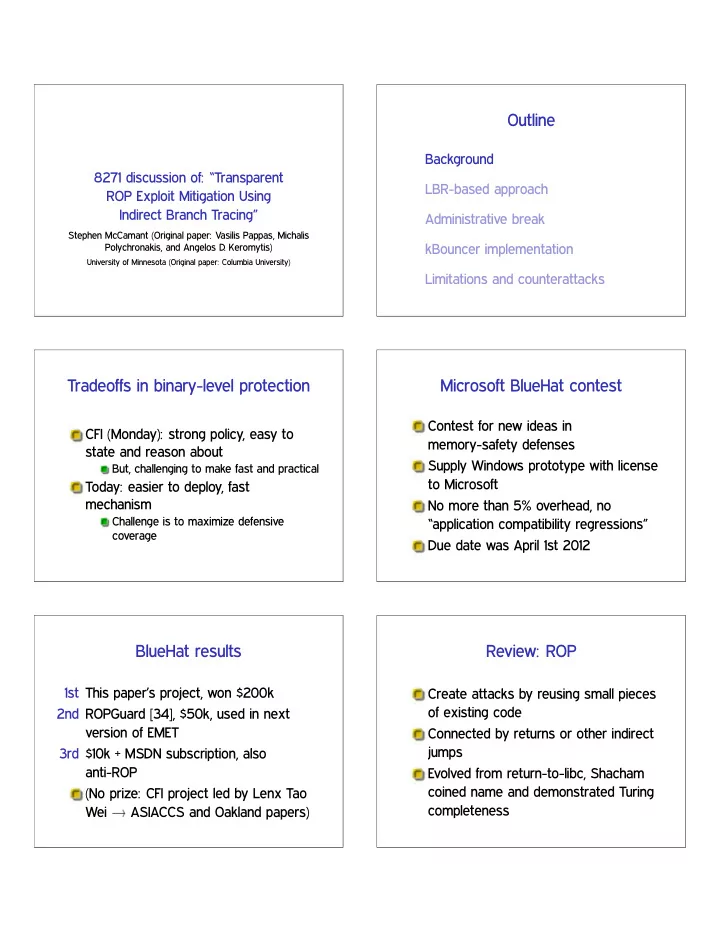
8271 discussion of: “Transparent ROP Exploit Mitigation Using Indirect Branch Tracing”
Stephen McCamant (Original paper: Vasilis Pappas, Michalis Polychronakis, and Angelos D. Keromytis)
University of Minnesota (Original paper: Columbia University)
Outline
Background LBR-based approach Administrative break kBouncer implementation Limitations and counterattacks
Tradeoffs in binary-level protection
CFI (Monday): strong policy, easy to state and reason about
But, challenging to make fast and practical
Today: easier to deploy, fast mechanism
Challenge is to maximize defensive coverage
Microsoft BlueHat contest
Contest for new ideas in memory-safety defenses Supply Windows prototype with license to Microsoft No more than 5% overhead, no “application compatibility regressions” Due date was April 1st 2012
BlueHat results
1st This paper’s project, won $200k 2nd ROPGuard [34], $50k, used in next version of EMET 3rd $10k + MSDN subscription, also anti-ROP (No prize: CFI project led by Lenx Tao Wei ✦ ASIACCS and Oakland papers)
Review: ROP
Create attacks by reusing small pieces
- f existing code