SLIDE 1
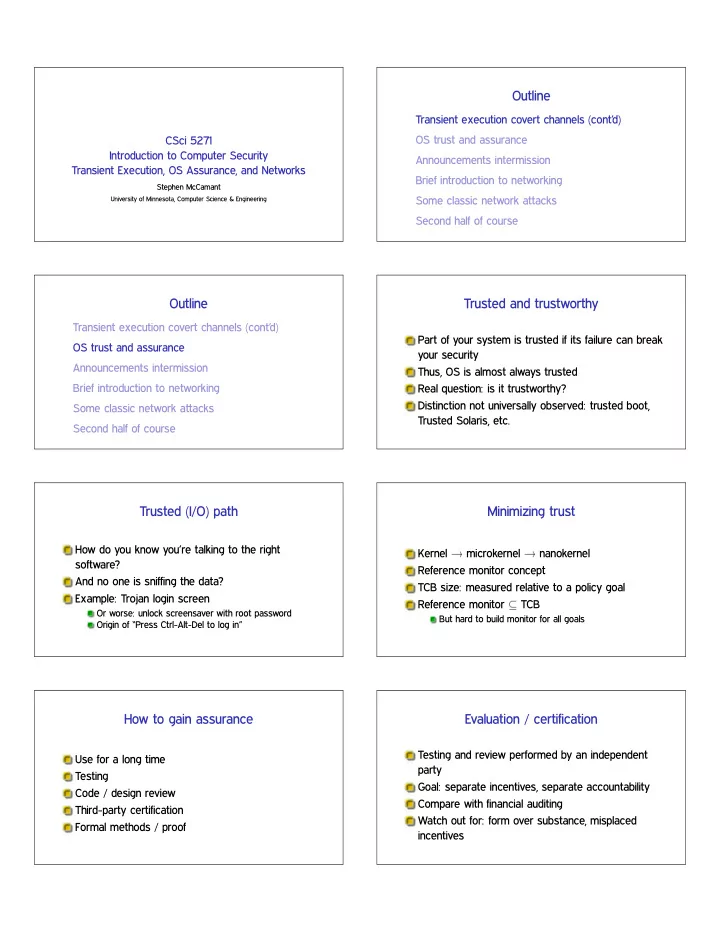
CSci 5271 Introduction to Computer Security Transient Execution, OS Assurance, and Networks
Stephen McCamant
University of Minnesota, Computer Science & Engineering
Outline Transient execution covert channels (contd) OS trust and - - PDF document
Outline Transient execution covert channels (contd) OS trust and assurance CSci 5271 Introduction to Computer Security Announcements intermission Transient Execution, OS Assurance, and Networks Brief introduction to networking Stephen
University of Minnesota, Computer Science & Engineering