1 Database Security
Simone Fischer-Hübner
Applied Security, DAVC17
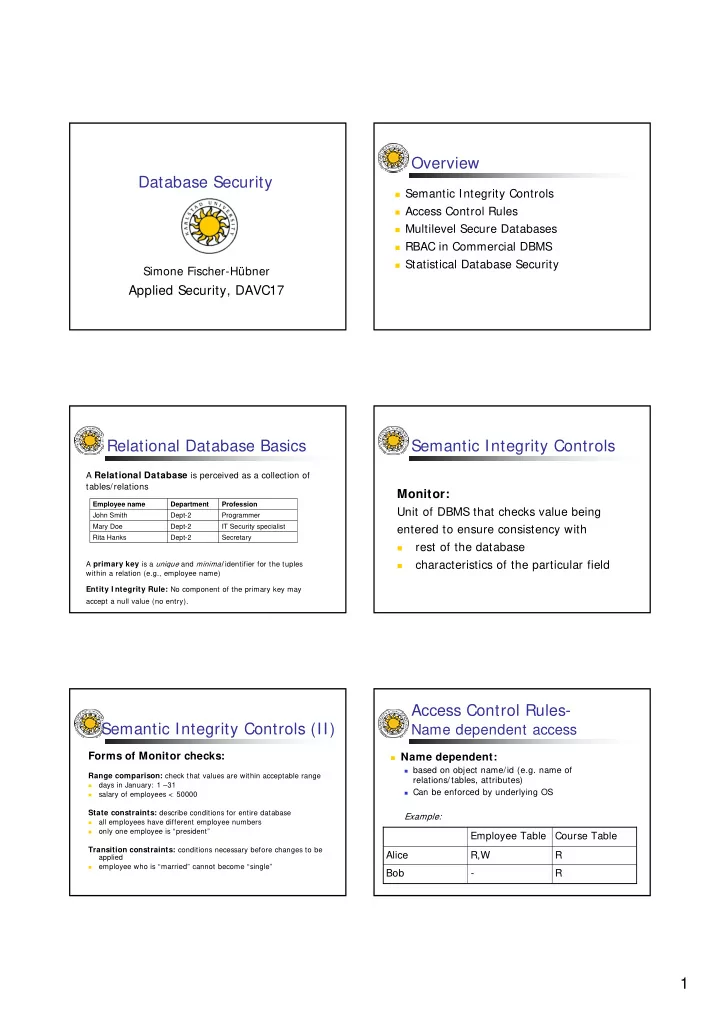
Overview
Semantic Integrity Controls Access Control Rules Multilevel Secure Databases RBAC in Commercial DBMS Statistical Database Security
Relational Database Basics
A Relational Database is perceived as a collection of tables/relations
Secretary Dept-2 Rita Hanks IT Security specialist Dept-2 Mary Doe Programmer Dept-2 John Smith Profession Department Employee name A primary key is a unique and minimal identifier for the tuples within a relation (e.g., employee name)
Entity I ntegrity Rule: No component of the primary key may accept a null value (no entry).
Semantic Integrity Controls
Monitor:
Unit of DBMS that checks value being entered to ensure consistency with
- rest of the database
- characteristics of the particular field
Semantic Integrity Controls (II)
Forms of Monitor checks:
Range comparison: check that values are within acceptable range
- days in January: 1 –31
- salary of employees < 50000
State constraints: describe conditions for entire database
- all employees have different employee numbers
- nly one employee is “president”
Transition constraints: conditions necessary before changes to be applied
- employee who is “married” cannot become “single”
Access Control Rules-
Name dependent access
Name dependent:
based on object name/id (e.g. name of
relations/tables, attributes)
Can be enforced by underlying OS
Example:
R
- Bob