SLIDE 1 ✂✁ ✄ ✁ ☎ ✁ ✆ ✝✟✞✠✁ ✡ ✁ ☛ ✝ ☞✌✝ ✡ ✄ ✍ ✎ ✆ ✄ ✝ ☞✏✆ ✑ ✒✔✓ ✒✟✁ ☞✌✁ ✕ ✖ ✗ ✆ ✘ ✡ ✁ ✡✌✁ ✡ ✙✛✚ ✓ ✜✢✝ ✘ ✖ ✕ ✝ ✣ ✤✦✥★✧✂✩✫✪✠✬✂✭✫✮✯✩✫✧✱✰✳✲✯✥★✴★✵✷✶✳✸✹✪✠✬✂✺✳✬✂✻✫✩✫✪✠✬✂✭✫✮ ✼✾✽❀✿❂❁❄❃ ❅✠❆✂❇❉❈✢❊✱✿❂❋❀●❍❈✢■ ✂✁ ✄ ✁ ☎ ✁ ✆ ✝✟✞✠✁ ✡ ✁ ☛ ✝ ☞✌✝ ✡ ✄ ✍ ✎ ✆ ✄ ✝ ☞✏✆ ✑ ✒✔✓ ✒✟✁ ☞✌✁ ✕ ✖ ✗ ✆ ✘ ✡ ✁ ✡✌✁ ✡ ✙✛✚ ✓ ✜✢✝ ✘ ✖ ✕ ✝ ❏ ✶✳❑✹✥★✴★❑✹✬✂✥★▲▼✭✂◆❖✰✳✲✯✥★✴★✵✷✶✳✸✹✪✠✬✢✺✳✬✂✻✫✩✫✪✠✬✂✭✫✮
❖
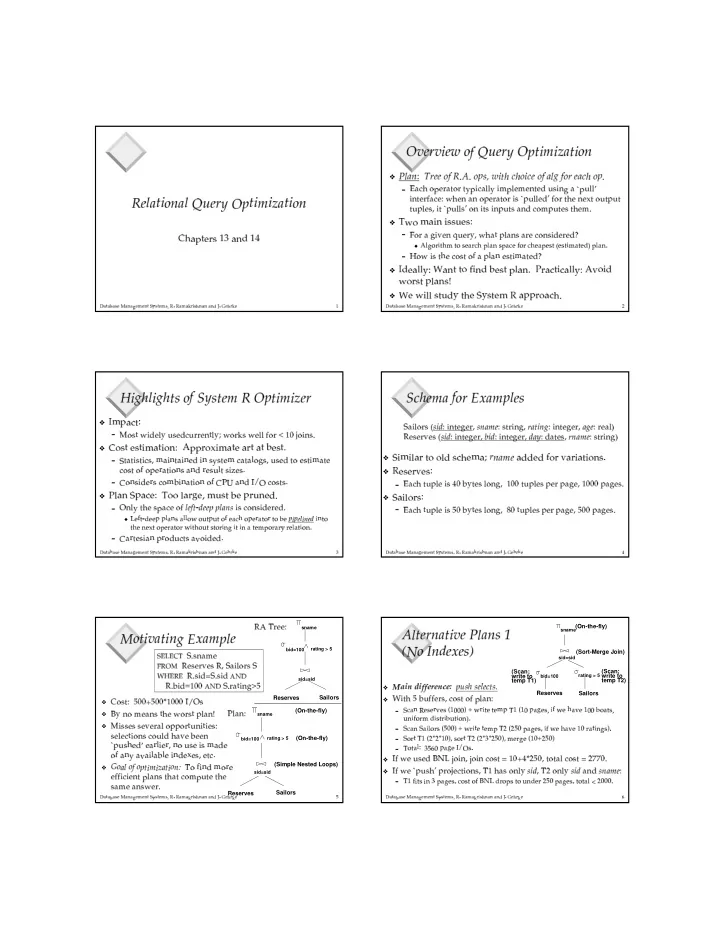
P❘◗ ❙✌❚❱❯ ❲❂❳✂❨✢❨❬❩ ❭❬❪❴❫ ❵✹❫❂❩✌❛❝❜✢❞❝❡✹❢ ❣ ❤❥✐✛❤❂❩✌❢ ✐❦❨✫❩ ❭❬❙✌◗ ❧✫❭✂❩✌❳❬❨✢❙✌✐✛❤✱❩✌❛❂❫ ♠♦♥q♣✌r✢s✹t✈✉❝✇✛① ♣✌② t✈①★② ③✠✉❝④ r✢♣✌⑤ ⑤ ③✾④ ⑥✱✉❝⑤ ✇✛⑥✱✇✛⑦❂② ✇✛⑧❥⑨❝⑩✔④ ⑦❂❶✾♣❬❷ ✉❝⑨q⑤ ⑤ ❸ ④ ⑦❂② ✇✛① ❹ ♣✌r✢✇✛❺✌❻✹s❂✇✛⑦✹♣✌⑦✹t✈✉❝✇✛① ♣✌② t✈①★④ ⑩❀❷ ✉❂⑨q⑤ ⑤ ✇✛⑧q❸✌❹ t✈①★② s❂✇✫⑦❂✇✛❼✌②❂t✈⑨q② ✉❝⑨q② ② ⑨q✉❝⑤ ✇✛⑩✔❽✌④ ②❂❷ ✉❂⑨q⑤ ⑤ ⑩✔❸✏t✈⑦✹④ ② ⑩❀④ ⑦❂✉❝⑨q② ⑩❾♣✌⑦❂⑧❿r✢t✈⑥✱✉❝⑨q② ✇✛⑩❀② s❂✇✛⑥✱➀❖
➁❘➂➄➃❉➅ ✿❂➆ ❋➄➆ ❇❦❇❦➇❄❅✠❇ ❯ ♠♦➈✠t✈①★♣❬❶✠④ ➉✠✇✛⑦✹➊✠⑨q✇✛① ③✠❽❦❻✹s❂♣✌②❂✉❝⑤ ♣✌⑦❂⑩❾♣✌① ✇✫r✢t✈⑦❂⑩✔④ ⑧q✇✛① ✇✛⑧q➋ ◆ ➌❾➍ ➎✂➏✂➐ ➑ ➒ ➓✌➔✯➒ ➏❾→ ➣✟↔✟➐ ↕ ➓❄➙✌➍ ↔ ➛❘→ ➙✏↔ ↕ ➣❝➜ ➏✂➐✏↕ ➓✌➣✟↔ ➙✌➣ → ➒✌➝ ➣ → ➒ ➑ ➔❬↔✟➒ ➣✟➞❦➟✂➙✌➍ ↔ ➛✈➠ ♠♦➡✹t✈❻➢④ ⑩❀② s❂✇✫r✢t✈⑩✔②❂t✈❹❂♣❬✉❝⑤ ♣✌⑦✹✇✛⑩✔② ④ ⑥❥♣✌② ✇✛⑧q➋❖
➤- ❘❅✠✿❂➥
- ➂➄➃
❖
➧ ❅ ➂ ➆ ➥ ➥➺❇❦❃ ➇❄●❘➦✯❃ ✽❀❅❿➻q➦★❇❦❃ ❅ ➅➽➼ ✿❂❁❄❁❄❆ ➃ ✿❂➲✌✽✾➭ ✂✁ ✄ ✁ ☎ ✁ ✆ ✝✟✞✠✁ ✡ ✁ ☛ ✝ ☞✌✝ ✡ ✄ ✍ ✎ ✆ ✄ ✝ ☞✏✆ ✑ ✒✔✓ ✒✟✁ ☞✌✁ ✕ ✖ ✗ ✆ ✘ ✡ ✁ ✡✌✁ ✡ ✙✛✚ ✓ ✜✢✝ ✘ ✖ ✕ ✝ ➾ ➚✳✬ ➪➄➶✹✧✂✬ ➪➄➶✹✪✠➹➘✭✂◆❖➴✯✵✹➹★✪✠✥★✺➷✤➬✶➮✸✹✪✠✬✂✺✳✬✂✻✫✥★✴❖
➤ ➅ ❁❄✿❂➲✌❃ ❯ ♠♦➱✃t✈⑩✔②❂❻✹④ ⑧q✇✛⑤ ③❐⑨q⑩✔✇✛⑧qr✔⑨q① ① ✇✛⑦❂② ⑤ ③✠❒✌❻✹t✈① ❮✠⑩❀❻✹✇✛⑤ ⑤✏❹ t✈①★❰❿Ï❦Ð❬Ñ t✈④ ⑦❂⑩✔➀❖
✼ ➃ ❇❦❃❾❅✠❇❦❃ ➆ ➅ ✿❂❃ ➆ ➃ ❋ ❯❬➳ ❁❄❁❄❆ ➃★Ò ➆ ➅ ✿❝❃ ❅❿✿❂❆✂❃❾✿❂❃❾➩★❅✠❇❦❃✌➭ ♠♦Ó✏② ♣✌② ④ ⑩✔② ④ r✢⑩✔❽✌⑥❥♣✌④ ⑦❂② ♣✌④ ⑦❂✇✛⑧❥④ ⑦✹⑩✟③✠⑩✔② ✇✛⑥❍r✔♣✌② ♣✌⑤ t✈❶✈⑩✔❽✌⑨❝⑩✔✇✛⑧❥② t❐✇✛⑩✔② ④ ⑥❥♣✌② ✇ r✢t✈⑩✔②❂t✈❹❝t✈✉❝✇✛① ♣✌② ④ t✈⑦❂⑩❾♣✌⑦❂⑧❥① ✇✛⑩✟⑨q⑤ ②❂⑩✔④ Ô✌✇✛⑩✟➀ ♠♦Õ❘t✈⑦❂⑩✔④ ⑧q✇✛① ⑩❀r✢t✈⑥✱Ö✠④ ⑦✠♣✌② ④ t✈⑦✹t✈❹❂Õ❘×❝ØÙ♣✌⑦❂⑧❥Ú Û❝ÜÝr✢t✈⑩✔② ⑩✔➀❖
➯❄➥ ✿❂❋➄➻q❁❄✿❂➲✌❅ ❯✫➁❘➃➺➃ ➥ ✿❂❆✂Þ★❅✠ß ➅ ➇❄❇✌❃❾➩★❅❿❁❘❆✂➇❄❋❀❅✠●❿➭ ♠♦Ü❱⑦❂⑤ ③✾② s❂✇✫⑩✔✉❝♣✌r✢✇✫t✈❹✠à á â✟ã ä å✌á á æ❬æ✌à ç✢è✠é❾④ ⑩❾r✢t✈⑦❂⑩✔④ ⑧q✇✛① ✇✛⑧q➀ ◆ ê✌➣ ➜ ➒ ë ➞❦➣✟➣ ➙❘➙✌➍ ↔ ➛✌→❂↔✟➍ ➍ ➏✢ì❉➏✢í✌➒ ➙✌í✌➒✛➏✂➜✛➣✟↔✟↕ ➓❘➏✢➙✌➣ ➐ ↔✟➒ ➏✂➐✏➒ ➏➺î❦➣✠ï✛ð ï✂ñ ò ð ó✂ñ ô ➑ ➛✌➒ ➏ ➒ ➓✌➣❂➛✌➣ õ✔➒✛➏✢➙✌➣ ➐ ↔✟➒ ➏✂➐✌ì❘➑ ➒ ➓✌➏✂í✌➒✛→ ➒ ➏✂➐ ➑ ➛✌➎❾➑ ➒✛➑ ➛✫↔q➒ ➣ ➔❘➙✌➏✂➐ ↔✟➐ ö❀➐ ➣ ➍ ↔✟➒ ➑ ➏✢➛✈➠ ♠♦Õ❘♣✌① ② ✇✛⑩✔④ ♣✌⑦✹✉❝① t✈⑧❝⑨qr✢② ⑩❾♣✌➉✠t✈④ ⑧q✇✛⑧q➀ ✂✁ ✄ ✁ ☎ ✁ ✆ ✝✟✞✠✁ ✡ ✁ ☛ ✝ ☞✌✝ ✡ ✄ ✍ ✎ ✆ ✄ ✝ ☞✏✆ ✑ ✒✔✓ ✒✟✁ ☞✌✁ ✕ ✖ ✗ ✆ ✘ ✡ ✁ ✡✌✁ ✡ ✙✛✚ ✓ ✜✢✝ ✘ ✖ ✕ ✝ ÷ ➴✯ø❀➶✹✥★✺✳✩✱◆✫✭✫✴➘ùÙú✹✩✫✺✳✸✹✧✂✥★➹❖
➻q➆ ➅ ➆ ➥ ✿❂❆❬❃ ➃❉➃ ➥- ➫❇❦➲✌✽❀❅
❖
➼ ❅✠❇❦❅✠❆ ➵ ❅✠❇ ❯ ♠♦♥q♣✌r✢s✹② ⑨q✉❝⑤ ✇✫④ ⑩❾ý❦Ð❬Ö✠③✠② ✇✛⑩❾⑤ t✈⑦❂❶✠❽❬Ï❦Ð❦Ð❴② ⑨q✉❝⑤ ✇✛⑩❾✉❝✇✛①★✉❝♣✌❶✠✇✛❽❦Ï❦Ð✌Ð❦Ð❴✉❂♣✌❶✠✇✛⑩✟➀❖
➻q✿❂➆ ➥ ➃ ❆✂❇ ❯ ♠♦♥q♣✌r✢s✹② ⑨q✉❝⑤ ✇✫④ ⑩❾þ❦Ð❬Ö✠③✠② ✇✛⑩❾⑤ t✈⑦❂❶✠❽❬ÿ❦Ð❴② ⑨q✉❝⑤ ✇✛⑩❾✉❂✇✛①★✉❝♣✌❶✠✇✛❽❦þ❦Ð✌Ð❬✉❝♣❦❶✠✇✛⑩✔➀ Ó✏♣✌④ ⑤ t✈① ⑩✁ é ✂ å✏❺❦④ ⑦❂② ✇✛❶✠✇✛① ❽❦é è✠ç☎✄❱á ❺✌⑩✔② ① ④ ⑦❂❶✠❽✝✆ ç✢ã ✂ è✟✞✏❺✌④ ⑦❂② ✇✛❶✠✇✛① ❽❦ç✠✞✌á✟❺❦① ✇✛♣✌⑤ ✡ ☛ ✇✛⑩✔✇✛① ➉✠✇✛⑩✁ é ✂ å✌❺✌④ ⑦❂② ✇✛❶✠✇✛① ❽✌☞✍✂ å✏❺❦④ ⑦❂② ✇✛❶✠✇✛① ❽❦å✌ç✠✎✏❺✛⑧q♣✌② ✇✛⑩ ❽✝✆ è✠ç☎✄❱á ❺✌⑩✔② ① ④ ⑦❂❶✏✡ ✂✁ ✄ ✁ ☎ ✁ ✆ ✝✟✞✠✁ ✡ ✁ ☛ ✝ ☞✌✝ ✡ ✄ ✍ ✎ ✆ ✄ ✝ ☞✏✆ ✑ ✒✔✓ ✒✟✁ ☞✌✁ ✕ ✖ ✗ ✆ ✘ ✡ ✁ ✡✌✁ ✡ ✙✛✚ ✓ ✜✢✝ ✘ ✖ ✕ ✝ ✑ ✒➷✭✫✪✠✬✂❑✹✩✫✪✠✬✂✮❐➪ ùÙú✹✩✫✺✳✸✹✧✂✥❖
Õ❘t✈⑩✔② ❺❬þ❦Ð✌Ð✌✓❝þ✌Ð❦Ð✕✔ Ï✌Ð❦Ð❦Ð❴Ú ÛqÜ❱⑩❖
✖ ③✾⑦❂t❐⑥✱✇✂♣✌⑦❂⑩❀② s❂✇✫❻✹t✈① ⑩✔②❂✉❝⑤ ♣✌⑦✘✗❖
➱✃④ ⑩✔⑩✔✇✛⑩❾⑩✔✇✛➉✠✇✛① ♣✌⑤✈t✈✉❝✉❝t✈① ② ⑨q⑦❂④ ② ④ ✇✛⑩✔❺ ⑩✔✇✛⑤ ✇✛r✢② ④ t✈⑦❂⑩❀r✢t✈⑨q⑤ ⑧❥s❂♣✌➉✠✇❘Ö✠✇✛✇✛⑦ ❷ ✉❝⑨q⑩✔s❂✇✛⑧q❸✏✇✂♣✌① ⑤ ④ ✇✛① ❽✌⑦❂t❐⑨q⑩✔✇❘④ ⑩❀⑥❥♣✌⑧q✇ t✈❹❝♣✌⑦❂③❐♣✌➉✈♣✌④ ⑤ ♣✌Ö✠⑤ ✇✫④ ⑦❂⑧q✇✛❼✌✇✛⑩✔❽❦✇✛② r✢➀❖
✙✛✚ ç✢à ✚ â ✚ æ✌ã ✂ ✄✜✂ ✢✢ç✔ã ✂ ✚ è✏✣✥✤qt❐❹ ④ ⑦❂⑧❿⑥✱t✈① ✇ ✇✛❹ ❹ ④ r✢④ ✇✛⑦❂②❂✉❝⑤ ♣✌⑦❂⑩❀② s❂♣✌②❂r✢t✈⑥✱✉❂⑨q② ✇✫② s❂✇ ⑩✔♣✌⑥✱✇❘♣✌⑦❂⑩✔❻✹✇✛① ➀ ✦☎✧ ê ✧✕★✪✩ Ó✏➀ ⑩✔⑦✠♣✌⑥✱✇ ✫✍✬✏✭✯✮ ☛ ✇✛⑩✔✇✛① ➉✠✇✛⑩ ☛ ❽✌Ó✌♣✌④ ⑤ t✈① ⑩❀Ó ✰✲✱✳✧ ✬ ✧ ☛ ➀ ⑩✔④ ⑧✪✴qÓ✏➀ ⑩✔④ ⑧ ➌✯✵✁✶ ☛ ➀ Ö✠④ ⑧✪✴❝Ï✌Ð❦Ð ➌✷✵✳✶ Ó✌➀ ① ♣✌② ④ ⑦❂❶✏✸❝þReserves Sailors
sid=sid bid=100 rating > 5 sname
Reserves Sailors
sid=sid bid=100 rating > 5 sname
(Simple Nested Loops) (On-the-fly) (On-the-fly)
☛✯✹ ✤q① ✇✛✇✛❺ ×q⑤ ♣✌⑦❂❺ ✂✁ ✄ ✁ ☎ ✁ ✆ ✝✟✞✠✁ ✡ ✁ ☛ ✝ ☞✌✝ ✡ ✄ ✍ ✎ ✆ ✄ ✝ ☞✏✆ ✑ ✒✔✓ ✒✟✁ ☞✌✁ ✕ ✖ ✗ ✆ ✘ ✡ ✁ ✡✌✁ ✡ ✙✛✚ ✓ ✜✢✝ ✘ ✖ ✕ ✝ ✺ ✻ ✧✂✪✠✥★✴★✮✯✩✫✪✠✬✂❑✹✥✽✼Ù✧✂✩✫✮✯➹✿✾ ❀✏❁ ✭❃❂✠✮❅❄✹✥★ú✹✥★➹✷❆❖
❇❉❈✏❊ ❋❍●✟❊ ■ ■✝❏☎❑ ❏☎❋✏▲☎❏✠▼ æ✕◆✠é ❖❴é á à á P✟ã é ◗❖
❘ ④ ② s✹þ❬Ö✠⑨❝❹ ❹ ✇✛① ⑩✔❽❦r✢t✈⑩✔②❂t✈❹❂✉❝⑤ ♣✌⑦❂❺ ❙ ✦ ↕ ↔ ➛ ✬ ➣ → ➣ ➐ ❚❦➣ →❝➝ ❯ ❱✠❱❲❱✔➟✌❳❀ì❘➐ ➑ ➒ ➣❝➒ ➣ ➔❘➙ ✩ ❯➺➝ ❯ ❱q➙✏↔✟➎✂➣ → ❨✟➑ ➜✂ì❘➣❝➓✏↔ ❚❦➣❩❯ ❱❲❱❝î❦➏✂↔✟➒ → ❨ í❦➛✌➑ ➜ ➏✂➐ ➔✃➞❦➑ → ➒ ➐ ➑ î❦í✌➒ ➑ ➏✢➛✌➟ ➠ ❙ ✦ ↕ ↔ ➛ ✦ ↔✟➑ ➍ ➏✂➐ →❝➝ ❬✠❱✠❱✔➟✌❳❀ì❘➐ ➑ ➒ ➣❝➒ ➣ ➔❘➙ ✩✕❭ ➝ ❭ ❬☎❱q➙✏↔✟➎✂➣ → ❨✟➑ ➜✂ì❘➣❂➓✏↔ ❚❦➣❩❯ ❱➺➐ ↔✟➒ ➑ ➛✌➎✂→ ➟ ➠ ❙ ✦ ➏✂➐ ➒ ✩ ❯➺➝ ❭✠❪ ❭✠❪ ❯ ❱✔➟ ❨✟→ ➏✂➐ ➒ ✩✕❭ ➝ ❭✠❪ ❫✠❪ ❭ ❬✠❱✔➟ ❨✟➔✫➣ ➐ ➎✛➣➺➝ ❯ ❱☎❳ ❭ ❬☎❱✔➟ ❙ ✩ ➏✂➒ ↔✟➍ ❴ ❫ ❬✠❵✠❱q➙✏↔✟➎✂➣✪❛ ❜ ✭ → ➠❖
Ú ❹❝❻✹✇❘⑨q⑩✔✇✛⑧ ✖❞❝❢❡ Ñ t✈④ ⑦❂❽✌Ñ t✈④ ⑦✹r✢t✈⑩✔②✏✴❿Ï❦Ð✕✓❝ý✕✔ ❣❦þ✌Ð❦❽✌② t✈② ♣✌⑤✈r✢t✏⑩✔②✘✴✲❣✌❤✕❤❦Ð✌➀❖
Ú ❹❝❻✹✇❘❷ ✉❝⑨q⑩✔s❂❸✏✉❝① t✈Ñ ✇✛r✢② ④ t✈⑦❂⑩✔❽✕✤❝Ï❴s✠♣✌⑩❀t✈⑦❂⑤ ③❱é ✂ å✌❽✕✤❞❣❬t✈⑦❂⑤ ③❐é ✂ å❴♣✌⑦❂⑧✹é è✠ç✠✄❱á✟❺ ❙ ✩ ❯❝➜ ➑ ➒ →✠➑ ➛ ❫ ➙✏↔✟➎✂➣ → ❨✟↕ ➏✂→ ➒✛➏✂➜✝✐✕✵❄ê✫➞❦➐ ➏✢➙✌→✠➒ ➏★í❦➛✏➞❦➣ ➐ ❭ ❬☎❱q➙✏↔✟➎✂➣ → ❨✟➒ ➏✂➒ ↔✟➍✝❥ ❭ ❱❲❱✠❱✂➠Reserves Sailors
sid=sid bid=100 sname(On-the-fly) rating > 5
(Scan; write to temp T1) (Scan; write to temp T2) (Sort-Merge Join)