1 1
Software Engineering, M Young 5/15/00 1
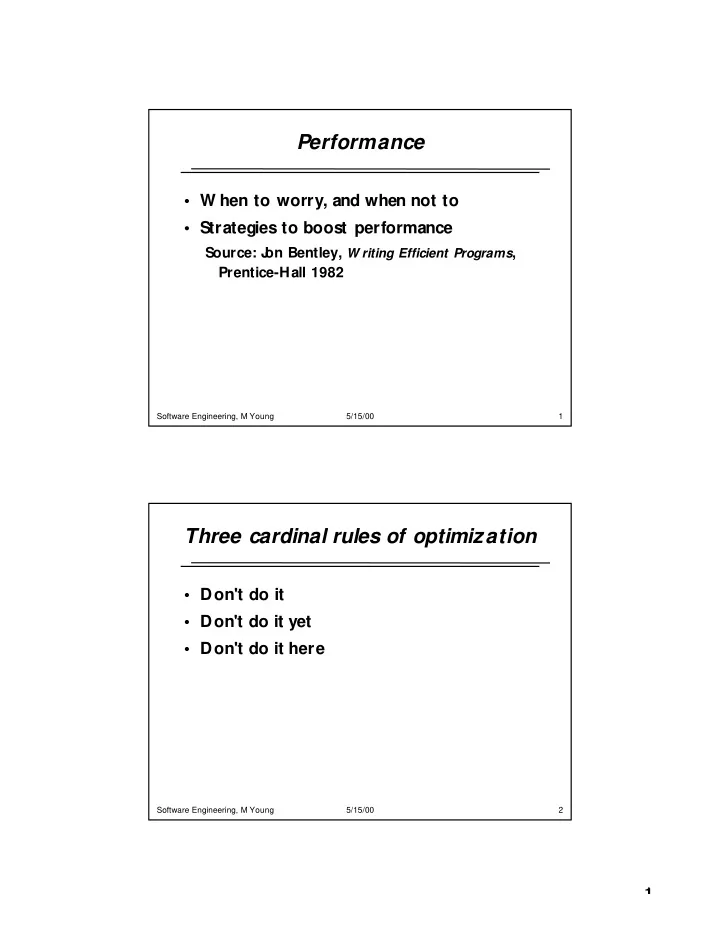
Performance
- W hen to worry, and when not to
- Strategies to boost performance
Source: J
- n Bentley, W riting Efficient Programs,
Prentice-Hall 1982
Software Engineering, M Young 5/15/00 2
Three cardinal rules of optimization
- Don't do it
- Don't do it yet
- Don't do it here