Preserving Privacy in Social Networks Against Neighborhood Attacks
Bin Zhou Jian Pei
School of Computing Science, Simon Fraser University 8888 University Drive, Burnaby, B.C., V5A1S6 Canada
{bzhou, jpei}@cs.sfu.ca Abstract— Recently, as more and more social network data has been published in one way or another, preserving privacy in publishing social network data becomes an important con-
- cern. With some local knowledge about individuals in a social
network, an adversary may attack the privacy of some victims
- easily. Unfortunately, most of the previous studies on privacy
preservation can deal with relational data only, and cannot be applied to social network data. In this paper, we take an initiative towards preserving privacy in social network data. We identify an essential type of privacy attacks: neighborhood attacks. If an adversary has some knowledge about the neighbors of a target victim and the relationship among the neighbors, the victim may be re-identified from a social network even if the victim’s identity is preserved using the conventional anonymization techniques. We show that the problem is challenging, and present a practical solution to battle neighborhood attacks. The empirical study indicates that anonymized social networks generated by our method can still be used to answer aggregate network queries with high accuracy.
- I. INTRODUCTION
Recently, as more and more social network data has been made publicly available [1], [2], [3], [4], preserving privacy in publishing social network data becomes an important concern. Is it possible that releasing social network data, even with individuals in the network aonymized, still intrudes privacy?
- A. Motivation Example
With some local knowledge about individual vertices in a social network, an adversary may attack the privacy of some
- victims. As a concrete example, consider a synthesized social
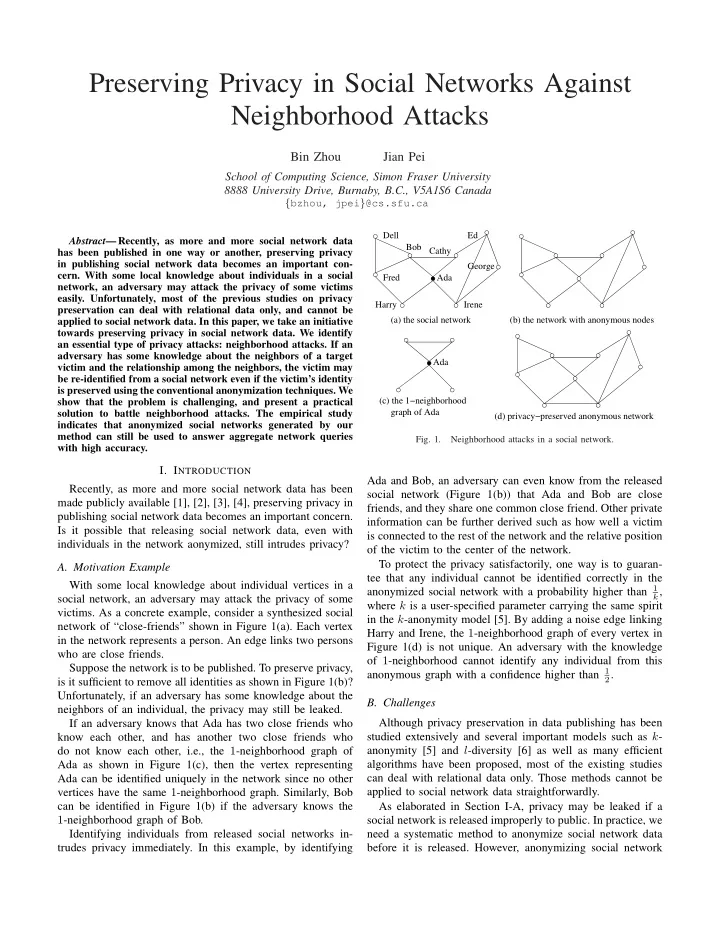
network of “close-friends” shown in Figure 1(a). Each vertex in the network represents a person. An edge links two persons who are close friends. Suppose the network is to be published. To preserve privacy, is it sufficient to remove all identities as shown in Figure 1(b)? Unfortunately, if an adversary has some knowledge about the neighbors of an individual, the privacy may still be leaked. If an adversary knows that Ada has two close friends who know each other, and has another two close friends who do not know each other, i.e., the 1-neighborhood graph of Ada as shown in Figure 1(c), then the vertex representing Ada can be identified uniquely in the network since no other vertices have the same 1-neighborhood graph. Similarly, Bob can be identified in Figure 1(b) if the adversary knows the 1-neighborhood graph of Bob. Identifying individuals from released social networks in- trudes privacy immediately. In this example, by identifying
Ada George (d) privacy−preserved anonymous network graph of Ada (c) the 1−neighborhood (b) the network with anonymous nodes Ada Bob Dell Fred Ed Cathy Irene Harry (a) the social network
- Fig. 1.
Neighborhood attacks in a social network.
Ada and Bob, an adversary can even know from the released social network (Figure 1(b)) that Ada and Bob are close friends, and they share one common close friend. Other private information can be further derived such as how well a victim is connected to the rest of the network and the relative position
- f the victim to the center of the network.
To protect the privacy satisfactorily, one way is to guaran- tee that any individual cannot be identified correctly in the anonymized social network with a probability higher than 1
k,
where k is a user-specified parameter carrying the same spirit in the k-anonymity model [5]. By adding a noise edge linking Harry and Irene, the 1-neighborhood graph of every vertex in Figure 1(d) is not unique. An adversary with the knowledge
- f 1-neighborhood cannot identify any individual from this
anonymous graph with a confidence higher than 1
2.
- B. Challenges
Although privacy preservation in data publishing has been studied extensively and several important models such as k- anonymity [5] and l-diversity [6] as well as many efficient algorithms have been proposed, most of the existing studies can deal with relational data only. Those methods cannot be applied to social network data straightforwardly. As elaborated in Section I-A, privacy may be leaked if a social network is released improperly to public. In practice, we need a systematic method to anonymize social network data before it is released. However, anonymizing social network