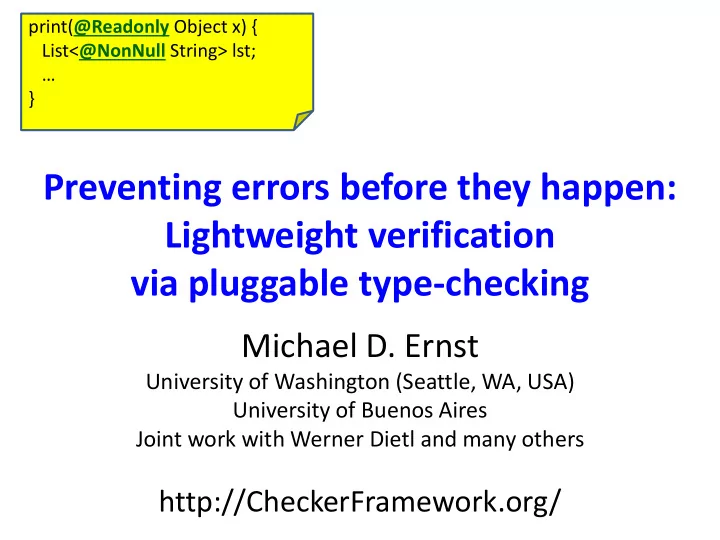
Preventing errors before they happen: Lightweight verification via pluggable type-checking
Michael D. Ernst
University of Washington (Seattle, WA, USA) University of Buenos Aires Joint work with Werner Dietl and many others
http://CheckerFramework.org/
print(@Readonly Object x) { List<@NonNull String> lst; … }