Private Information Retrieval
- ver ICN
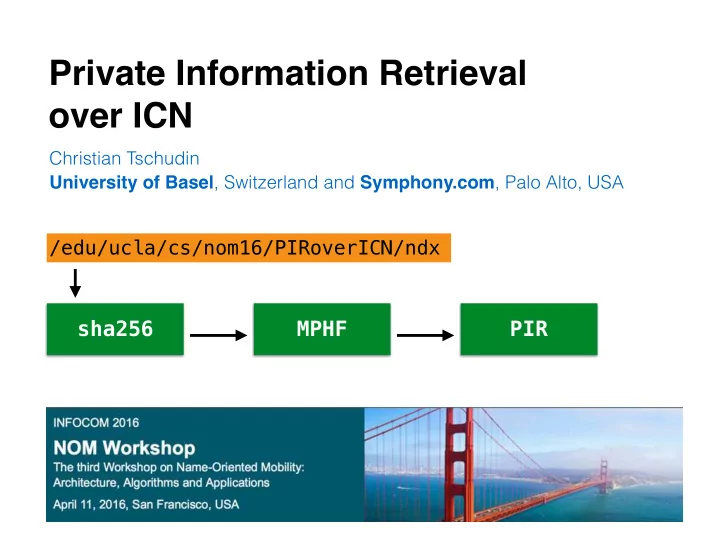
/edu/ucla/cs/nom16/PIRoverICN/ndx
sha256 MPHF PIR
Christian Tschudin University of Basel, Switzerland and Symphony.com, Palo Alto, USA
Private Information Retrieval over ICN Christian Tschudin - - PowerPoint PPT Presentation
Private Information Retrieval over ICN Christian Tschudin University of Basel , Switzerland and Symphony.com , Palo Alto, USA /edu/ucla/cs/nom16/PIRoverICN/ndx sha256 MPHF PIR Overview How to lookup secrets over public NDN?
/edu/ucla/cs/nom16/PIRoverICN/ndx
Christian Tschudin University of Basel, Switzerland and Symphony.com, Palo Alto, USA
… in many forms
/edu/ucla/cs/nom16/PIRoverICN/ndx
sha256 MPHF PIR
/edu/ucla/cs/nom16/PIRoICN/ndx sha256 MPHF PIR {nameless} The_Content
non-colluding servers
k servers 1 q k client a 1 a k n b ... a L l 1 a L k q
non-colluding servers
L and mphf PIR_lookup1(pos) PIR_lookup2(pos) publisher done get(mphf) mphf pos=mphf(h) lookup(h) d1 d2 init(loc1,loc2) d=combine(d1,d2) d PIR2 PIR1 app client lib
dir1 = private_lookup(“/edu/ucla/cs“ + hash(“.”)); // locator dir2 = private_lookup(“/edu/ucla/cs“ + hash(dir1 + "nom16")); dir3 = private_lookup(“/edu/ucla/cs“ + hash(dir2 + "venue"));
SSL means you trust that endpoint - can we avoid this? —> from passive storage to PIR servers, and other forms of name rewriting (never request the same hash value twice)