Security
in
Wireless Sensor Networks
2
Introduction
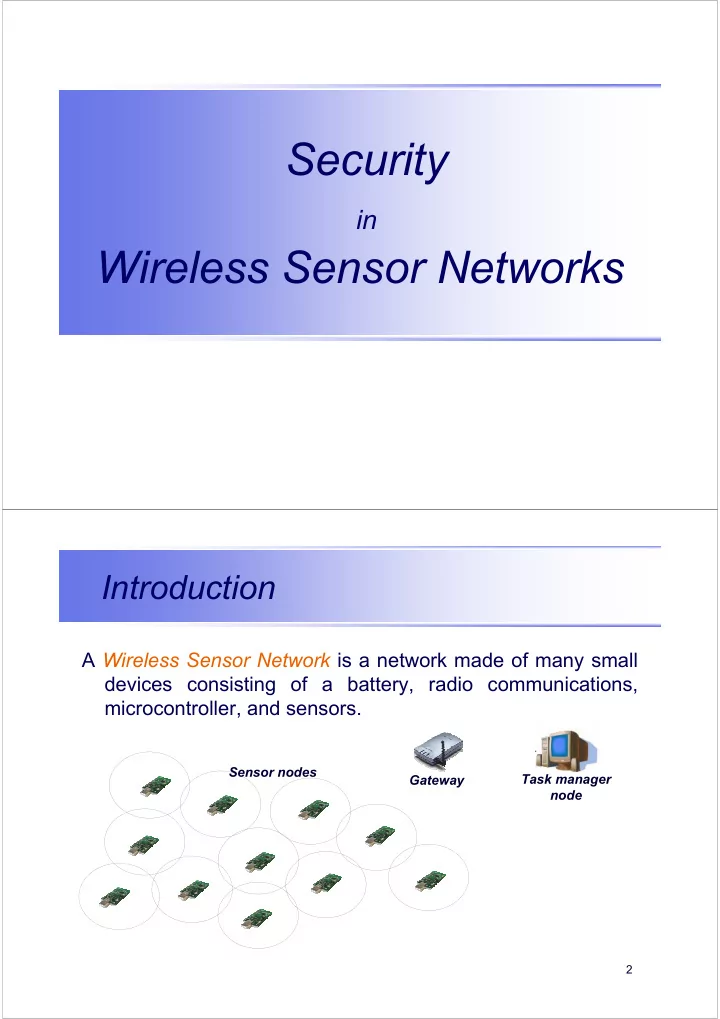
A Wireless Sensor Network is a network made of many small devices consisting of a battery, radio communications, microcontroller, and sensors.
Gateway Sensor nodes Task manager node
Security in Wireless Sensor Networks Introduction A Wireless - - PDF document
Security in Wireless Sensor Networks Introduction A Wireless Sensor Network is a network made of many small devices consisting of a battery, radio communications, microcontroller, and sensors. Sensor nodes Task manager Gateway node 2
2
A Wireless Sensor Network is a network made of many small devices consisting of a battery, radio communications, microcontroller, and sensors.
Gateway Sensor nodes Task manager node
3
The sensor nodes cooperate to monitor enviromental phenomena.
detect phenomenon routing Gateway Sensor nodes Task manager node
4
– Military applications – Enviromental applications – Home applications – Health applications – Automotive applications – …
5
equipment and ammunition
forces and terrain
chemical attack detection and reconnaissance
6
Flood / Forest fire detection Precision agriculture Ecosystems
NY Times, May 10, 2005
Habitat Monitoring
7
Home automation Structural Monitoring
Kajima-Shizuoka Building – Japan
8
Health Care Monitoring of Mobile Patients. (Source: ISTI & IFC--CNR, Pisa, Italy). BASUMA (BMWA)-Germany
9
RUNES 10
– Distributed and large-scale networks
connectivity, task
– Hostile Environment
– Limited Resources
11
– The network topology may change very frequently
controlled robotic mobility
– The network must be reconfigurable
12
Capabilities Size, Power Consumption, Cost
PC Notebook Smartphone Mote
13 TI MSP430 –48kB code –10KB data Low-power radio: 250 kbps Integrated sensor ATmega128 –128kB code –4kB data Low-power radio: 40kbps Simple sensors ATmega163 –16kB code –1k B data Low-power radio: 10kbps Simple sensors Small µ-controller –8kB code –512 B data Low-power radio: 10kbps Simple sensor Mica2 Mote
Evolution
WeC 99 “Smart Rock” Dot 9/01 Telos Mote 14
–Autonomous –Mobile –Flying –Wearable
Medusa MK-2 (UCLA) iBadge (UCLA) Heliomote (UCLA)
STARGATE PACKBOT
Data Mule (UCLA)
MOTE Data Storage Path Planning
Helicopter Imager (UCLA) RagoBot (UCLA)
RAiN (Pisa)
15
Data Link Layer Physical Layer Network Layer Application Layer Data Link Layer Physical Layer Network Layer Application Layer
16
The physical layer is responsible for:
Open research issues:
propagation effects
Data Link Layer Physical Layer Network Layer Application Layer
17
Data Link Layer Physical Layer Network Layer Application Layer
The data link layer is responsible for:
Open research issues:
18
The network layer is responsible for:
presence of node failure
networks (i.e. Internet).
Open issues:
Data Link Layer Physical Layer Network Layer Application Layer
19
The application layer is responsible for:
Open issues:
advertisement protocol
dissemination
Data Link Layer Physical Layer Network Layer Application Layer
20
Security Requirements:
Data Link Layer Physical Layer Network Layer Application Layer
21
– Secure Network Communication
– Group-key management
– Secure Localization – Secure Time Synchronization – Secure Data Processing
22
23
– Asymmetric cryptography:
– Symmetric cryptography:
– Commercial standards for Motes
24
The amount of computational energy consumed by a security function is determined by:
Public key cryptographic algorithms such as RSA are computationally intensive:
perform a single security operation
25
Execution times for 2x (mod p) with p prime number (modulus) and x which ranges from 112 to 768 bit on MICA2 mote [Malan04]
As we can see, a single exponentiation could take 5 minutes !
26
3.7 s 512-bit 14.5 s 1024-bit 8.0 s 768-bit Verification time (Hardware Platform: Mica) Module size n
Tiny Public-Key:
Verification operation by using RSA with exponent e=3 and module n
27
Elliptic curve cryptography (ECC)
– given the equation Q=kG, known G and Q (points), then find the integer k
? 512 15360 256 ? 384 7680 192 after 2030 256 3072 128 before 2030 224 2048 112 before 2010 160 1024 80 Secure until.. ECC (Key length in bit) RSA (Key length in bit) EQUIVALENT SECURITY (bit) 28
– EccM 2.0 [Malan04] :
– 34 seconds to generate ECC key pairs (Diffie-Hellmann) – 70 seconds to run the entire Diffie-Hellman protocol
– TinyECC [LiuNing05]:
– 7 seconds for digital signature of ECDSA – 14.2 seconds for signature verification of ECDSA
µcontroller’s language
29
Parallelization
– T trusted, U untrusted – N = 2U + 1: if this condition is met the verifier always picks the correct value
63.71 s 50.74 s 50.77 s EccM 2.0 with parallelization 101.01 s 50.74 s 50.77 s EccM 2.0 Signature verification Digital Signature Public key generation Mode
30
Re-implementation
written in nesC
ECDSA verification (multiple multiplication)
10.7 8.8 0.015 (200 bytes) 8.5 Time (sec) Tmote Sky
Time (sec) MICAz Function 14.293 ECDSA Verification 7.074 ECDSA Signature
31
Hardware suppport – Hasegawa, Nakajima and Matsui [Hasegawa99]
– 0.15 seconds for digital signature of ECDSA – 0.63 seconds for verification of ECDSA
No multiplication/division Multiplication/division as hardware operation 27 istructions 91 instructions 8 Mhz 10 MHz TMote Sky M16C
32
– RC5 & SkypJack block-ciphers
– IV is needed to achieve semantic security – Same message looks different every time
IV m2 m1 c1 c2 Ek Ek Ek CBC-Mode
33
Mode CBC-CTS (Ciphertext Stealing)
even though plain text is not a multiple of block size
TinyOs-1.1.11 – 6.37 ms (RC5) – 2.40 ms (SkipJack)
34
SHA-1 is an hash function required by:
signature schemes)
It produces a hash value on 160 bit
13.24 128 8.911 64 4.69970 32 4.69970 16 4.66918 8 4.63867 4 Time (ms) Dimension (bytes) Performance on Tmote Sky
35
– Link Layer Security Architecture
– Support fine-grained mixed-mode usage
36
– TinySec-Auth
Sender Receiver < m, HMAC >
S m HMAC V m Yes/no HMAC
– Algorithm used for HMAC: SHA-1
37
– TinySec-AE
Receiver Sender < c, IV, HMAC >
c IV m2 m1 c1 c2 E E m E m IV c2 c1 m1 m2 D D c D
– Algorithm used for encryption: SkipJack in CBC-CTS mode
38
TinySec-AE:
IV
packet header (dest,AM,len,source) + counter (ctr) TinyOS: TinySec-Auth:
39
8% 28.8 68 44 TinySec-AE 1.5% 26.6 64 40 TinySec-Auth
63 39 TinyOS Increase Transmission Time (ms) Total Size (byte) Overhead (byte)
40
–AES is available in hardware
–Design similarities to TinySec:
–Design differences to TinySec
41
42
Approaches: – Centralized
– Distributed
subset of them
43
How many keys a node should maintain? – Globally shared secret key
– Secret key with base station (centralized approach)
– Pairwise secret key
collaborative data processing.
44
General Idea
Sink Node A KA KA KA KB KB KB KB KB Node B KAB
Some existing protocols: SNEP [Perrig 01], [Chen 00], [Undercoffer 02]
45
Wins:
– No leak of information.
Neutral:
– Loss for dynamic topologies.
Losses:
46
General idea
neighbors.
Key pool K1,K2,,..,Ks {K1,K3} K1 K3 R=2 {K3,K7} {K1,K5}
47
– Basic Scheme [Eschenauer02] – Extended to q-composite scheme [Chen03]
– Adaptive Random key distribution [Huang03]
– Blom scheme [Wenliang03]
– Polynomial key pools [Liu03]
48
Wins:
Neutral:
Losses:
49
General idea
node from the global key.
Key-setup phase Normal system Generate pairwise key from KG Erase KG No valid keys can be generated here
50
KAB = HKG(idA || PA || idB || PB) PX is the location [Ye04], physical attributes [Ganeriwal04a]
explicitly telling it to each other.
idA,PA Node A Node B idB,PB
51
– External adversary
– Internal adversary
erase KG as soon as possible.
Key-setup phase Normal system NO compromise during this phase
52
Wins:
Losses:
53
54
Problem
An outsider cannot eavesdrop or inject/modify messages.
Solution
All sensor nodes share a symmetric group-key used to encrypt/decrypt messages.
K
Sink
K K K K
K : group-key
55
Forward security
When a member leaves the group at time t* he cannot have access to communication after time t*.
LEAVING NODE
K
Sink
K K K K
K : group-key New group-key: K*
56
The sink must distribute the new group-key to all nodes except the leaving one.
received key – Chained Key Hash [Lamport81]
– Naive solution – S2RP: Scalable & Secure Rekeying Protocol [Dini05]
57
– Chained key hash
KN KN-1 KN-2 … K2 K1 K0 Generating Ki+1 =H(Ki) Revealing
58
– Naive solution
messages – The new key in encrypted with secret keys of nodes
LEAVING NODE
K
Sink
K K K K
K : group-key New group-key: K*
59
Each member stores the current-keys associated to the auxiliary-nodes on the path
K1
curr
K2
curr
K4
curr
K5
curr
D C B A K3
curr
K7
curr
K6
curr
E F G H
Leaf-node: correspond to the private key of a group member
KNKN-1 KN-2… K2 K1 K0 KNKN-1 KN-2… K2 K1 K0 KNKN-1 KN-2… K2 K1 K0
Auxiliary-node: associated to a key chain
curr i-th current-key (last-revealed
key)
curr Network-key
KN KN-1 KN-2 … K2 K1 K0
60
Path(D)={1,2,5} If D leave the group its keys are compromised
K1
curr
K2
curr
K4
curr
K5
curr
D C B A K3
curr
K7
curr
K6
curr
E F G H
KNKN-1 KN-2… K2 K1 K0 KNKN-1 KN-2… K2 K1 K0 KNKN-1 KN-2… K2 K1 K0 KNKN-1 KN-2… K2 K1 K0
The new keys are: K1
next,K2 next,K5 next so that
Ki
curr=H(Ki
next)
61
Secure distribution
KS C: E(KC,K5
next)
KS C: E(K5
next,K2 next)
KS A,B: E(K4
curr,K5
next)
KS A,B,C: E(K2
next,K1 next)
KS E,F,G,H: E(K3
curr,K1
next)
E(k,x) encryption of x with K
O(log n) messages SCALABILITY SCALABILITY
Knext1 Knext2 K4
curr
Knext5 D C B A K3
curr
K7
curr
K6
curr
E F G H
KNKN-1 KN-2… K2 K1 K0 KNKN-1 KN-2… K2 K1 K0 KNKN-1 KN-2… K2 K1 K0 KNKN-1 KN-2… K2 K1 K0
62
63
Node wants to communicate with multiple nodes simultaneously
the nodes
Nodes should be able to verify the identity of the sending node (NO malicious node).
What is the problem?
64
Abstract asymmetric nature using symmetric cryptography
– Use a different key in every slot.
KN KN-1 KN-2 … K2 K1 K0 Ki+1 =H(Ki) KN KN-1 KN-2 K2 K1 K0
slot 0 slot 1 slot 2 slot N-2 slot N-1 slot N
65
– The nodes stores only Ki-1: Ki is not yet known.
– Nodes, on receiving the key, authenticate key Ki and authenticate packet received in slot i As Ki was only known to the base station in slot i, nobody could have impersonated the base station in slot i.
m HMAC(Ki, m) message
66
Wins:
Neutral:
Losses:
67
68
– Mote-class attackers
– Laptop-class attackers
– Greater battery and processing power, memory – High-power radio transmitter, high bandwidth links to eavesdrop
69
– Outsider attackers
– Insider attackers
nodes
70
– Bogus routing information – Selective forward – Sinkhole attack – Sybil attack – Wormholes – HELLO flood attack
71
– Spoofed, altered, replayed routing info
– Ack spoofing
72
– Malicious nodes selectively forwards packets
1 3 2 4
Node A Node B
1 3 2 4
Node A
1 3 2 4
Node B
73
– Attacker tries to attract all traffic destined for the sink from nodes several hops away from itself
Solution: Authenticate routing info
sink
74
– A single node presents multiple identities to the other nodes Solution: Verify identities
Node has 5 neighbors
75
– The attacker tunnels msgs received in one part of the network and replays them in a different part
network
– This attack can be launched by insiders and outsiders
76
sink
Example: – Attacker A tunnels hello packets received from the sink and replay them to attacker B – Conseguence: many nodes cannot reach the sink Solution: avoid routing race conditions
77
– Nodes broadcast HELLO packets to announce themselves to their neighbors
Solution: Verify the bidirectionality of links
78
TinyOS beaconing
Attacks
all traffic in the network – HELLO attack
wormhole / sinkhole attacks
Hello packets
79
GeoRouting
Attacks
Broadcast messages:
1 2 2 1
Sensor node has 4 false neighbors
80
Minimum Cost Forwarding
base station)
Attacks
81
LEACH: Low-Energy Adaptive Clustering Hierarchy
to base station
consumption
Attacks
82
Bogus routing information, Sybil, HELLO floods Energy conserving topology maintenance Bogus routing information, selective forwarding, sinkholes, Sybil, wormholes Rumor routing Selective forwarding, HELLO floods Clustering based protocols (LEACH,TEEN,PEGASIS) Bogus routing information, selective forwarding, sinkholes, wormholes, HELLO floods Minimum cost forwarding Bogus routing information, selective forwarding, Sybil Geographic routing (GPSR,GEAR) Bogus routing information, selective forwarding, sinkholes, Sybil, wormholes, HELLO floods Directed diffusion and multipath variant Bogus routing information, selective forwarding, sinkholes, Sybil, wormholes, HELLO floods TinyOS beaconing
Relevant attacks Protocol
83
– Encryption & Authentication
– Verify neighbors’ identities
– Probabilistic routing
– Wormholes are hard to detect – Sinkholes are difficult to defend against in protocols that use advertise information (i.e. remaining energy)
84
Crypthographic mechanisms [Malan04] “A Public-Key Infrastructure for Key Distribution in TinyOS Based on Elliptic Curve Cryptography”. David J. Malan, Matt Welsh, and Michael D.
Communications and Networks. Santa Clara, California. October 2004. (http://www.eecs.harvard.edu/~malan/ ) [LiuNing05] An Liu, Peng Ning, "TinyECC: Elliptic Curve Cryptography for Sensor Networks (Version 0.1)", September , 2005http://discovery.csc.ncsu.edu/software/TinyECC/ . [Hasegawa05] “A Small and Fast Software Implementation of Elliptic Curve Cryptosystems over GF(p) on a 16-Bit Microcomputer”. TIEICE:IEICE Transactions on Communications/Electronics/Information and Systems, 1999. [SEC2] Certicom Research, “Sec 2: Recommended Elliptic Curve Domain Parameters” (Standard for efficient cryptography version 1.0), September 2002 (http://www.secg.org/download/aid-386/sec2_final.pdf ) [[TinyPK04] BBN Corporation. TinyPK Project. http://www.is.bbn.com/projects/lws-nest/
85
Key establishment & management [Chen00] M. Chen, W. Cui, V. Wen, A. Woo, “Secutiy and deployment issues in a sensor network” [Karlof03] Chris Karlof, Naveen Sastry and David Wagner, "TinySec: A Link Layer Security Architecture for Wireless Sensor Networks", Second ACM Conference on Embedded Networked Sensor Systems (SenSys 2004) [Undercoffer 02] Jeffery Undercoffer and Sasikanth Avancha and Anupam Joshi and John Pinkston (2002): “Security for Sensor Networks,” CADIP Research Symposium, 2002 [Perrig01] Adrian Perrig and Robert Szewczyk and J. D. Tygar and Victor Wen and David E. Culler (2001): “SPINS: Security Protocols for Sensor Networks,” Proceedings of Seventh Annual International Conference on Mobile Computing and Networks MOBICOM 2001, July 2001
86
[Eschenauerr02] Laurent Eschenauer and Virgil D. Gligor (2002): “A Key- Management Scheme for Distributed Sensor Networks,” Conference on Computer and Communications Security. Proceedings of the 9th ACM conference on Computer and communications security, Washington, DC, USA, 2002. [Chen03] H. Chan, A. Perrig, D. Song, “Random Key Predistribution Schemes for Sensor Networks”, IEEE Synposium on Security and Privacy, 2003. [Huang03] Adaptive random key distribution schemes for wireless sensor networks, WADIS 2003. [Wenliang03] W. Du, J. Deng, Y. Han, P. Varshney, “A pairwise key pre- distribution scheme for wireless sensor networks” [Liu03] D. Liu and P. Ning. Establishing pairwise keys in distributed sensor
Security, October 2003. [Lamport81] L. Lamport. Password authentication with insecure
1981.
87
[Dini05] G. Dini and I. Savino. Scalable and secure group rekeying in wireless sensor networks. Routing attacks [Karlof03b] C. Karlof, D. Wagner, “Secure routing in sensor networks: Attacks and countermeasures”, Elsevier AdHoc Networks journal, special issue on sensor network applications and protocols, May 2003