COMP 520 Winter 2016 Virtual Machines (1)
Virtual Machines
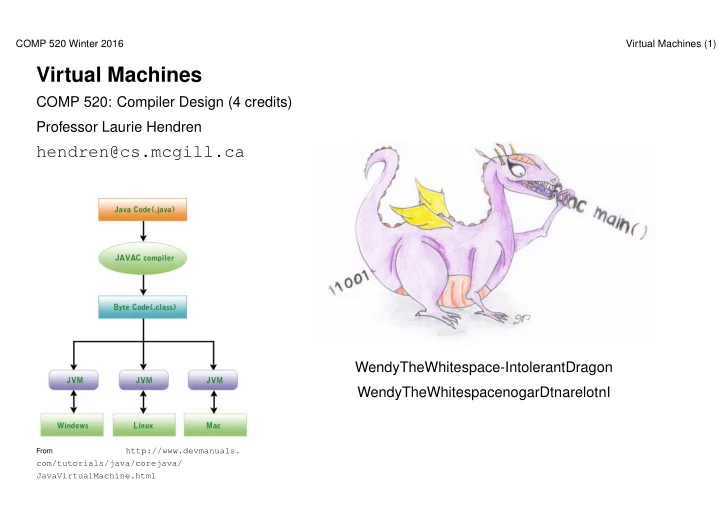
COMP 520: Compiler Design (4 credits) Professor Laurie Hendren
hendren@cs.mcgill.ca
From
http://www.devmanuals. com/tutorials/java/corejava/ JavaVirtualMachine.html
Virtual Machines COMP 520: Compiler Design (4 credits) Professor - - PowerPoint PPT Presentation
COMP 520 Winter 2016 Virtual Machines (1) Virtual Machines COMP 520: Compiler Design (4 credits) Professor Laurie Hendren hendren@cs.mcgill.ca WendyTheWhitespace-IntolerantDragon WendyTheWhitespacenogarDtnarelotnI From
COMP 520 Winter 2016 Virtual Machines (1)
From
http://www.devmanuals. com/tutorials/java/corejava/ JavaVirtualMachine.html
COMP 520 Winter 2016 Virtual Machines (2)
Abstract syntax trees Virtual machine code Interpreter Native binary code AOT-compile JIT-compile interpret
COMP 520 Winter 2016 Virtual Machines (3)
COMP 520 Winter 2016 Virtual Machines (4)
COMP 520 Winter 2016 Virtual Machines (5)
COMP 520 Winter 2016 Virtual Machines (6)
COMP 520 Winter 2016 Virtual Machines (7)
COMP 520 Winter 2016 Virtual Machines (8)
COMP 520 Winter 2016 Virtual Machines (9)
COMP 520 Winter 2016 Virtual Machines (10)
COMP 520 Winter 2016 Virtual Machines (11)
COMP 520 Winter 2016 Virtual Machines (12)
COMP 520 Winter 2016 Virtual Machines (13)
COMP 520 Winter 2016 Virtual Machines (14)
COMP 520 Winter 2016 Virtual Machines (15)
COMP 520 Winter 2016 Virtual Machines (16)
COMP 520 Winter 2016 Virtual Machines (17)
COMP 520 Winter 2016 Virtual Machines (18)
COMP 520 Winter 2016 Virtual Machines (19)
COMP 520 Winter 2016 Virtual Machines (20)
COMP 520 Winter 2016 Virtual Machines (21)
COMP 520 Winter 2016 Virtual Machines (22)
COMP 520 Winter 2016 Virtual Machines (23)
COMP 520 Winter 2016 Virtual Machines (24)
COMP 520 Winter 2016 Virtual Machines (25)
COMP 520 Winter 2016 Virtual Machines (26)
Java Compiler foo.java foo.class magic number (0xCAFEBABE) minor version/major version this class super class interfaces fields methods attributes constant pool access flags
COMP 520 Winter 2016 Virtual Machines (27)
COMP 520 Winter 2016 Virtual Machines (28)
COMP 520 Winter 2016 Virtual Machines (29)
COMP 520 Winter 2016 Virtual Machines (30)
COMP 520 Winter 2016 Virtual Machines (31)
.method public Abs(I)I // one int argument, returns an int .limit stack 2 // has stack with 2 locations .limit locals 2 // has space for 2 locals // --locals--
// [ o -3 ] [ * * ] iload_1 // [ o -3 ] [ -3 * ] ifge Label1 // [ o -3 ] [ * * ] iload_1 // [ o -3 ] [ -3 * ] iconst_m1 // [ o -3 ] [ -3 -1 ] imul // [ o -3 ] [ 3 * ] ireturn // [ o -3 ] [ * * ] Label1: iload_1 ireturn .end method
COMP 520 Winter 2016 Virtual Machines (32)
COMP 520 Winter 2016 Virtual Machines (33)
COMP 520 Winter 2016 Virtual Machines (34)
COMP 520 Winter 2016 Virtual Machines (35)
COMP 520 Winter 2016 Virtual Machines (36)
COMP 520 Winter 2016 Virtual Machines (37)
COMP 520 Winter 2016 Virtual Machines (38)
COMP 520 Winter 2016 Virtual Machines (39)
COMP 520 Winter 2016 Virtual Machines (40)
COMP 520 Winter 2016 Virtual Machines (41)
COMP 520 Winter 2016 Virtual Machines (42)
COMP 520 Winter 2016 Virtual Machines (43)
COMP 520 Winter 2016 Virtual Machines (44)
COMP 520 Winter 2016 Virtual Machines (45)
.method public member(Ljava/lang/Object;)Z .limit locals 2 // local[0] = o // local[1] = item .limit stack 2 // initial stack [ * * ] aload_0 // [ o * ] getfield Cons/first Ljava/lang/Object; // [ o.first *] aload_1 // [ o.first item] invokevirtual java/lang/Object/equals(Ljava/lang/Object;)Z // [ b * ] for some boolean b ifeq else_1 // [ * * ] iconst_1 // [ 1 * ] ireturn // [ * * ] else_1: aload_0 // [ o * ] getfield Cons/rest LCons; // [ o.rest * ] aconst_null // [ o.rest null] if_acmpne else_2 // [ * * ] iconst_0 // [ 0 * ] ireturn // [ * * ] else_2: aload_0 // [ o * ] getfield Cons/rest LCons; // [ o.rest * ] aload_1 // [ o.rest item ] invokevirtual Cons/member(Ljava/lang/Object;)Z // [ b * ] for some boolean b ireturn // [ * * ] .end method
COMP 520 Winter 2016 Virtual Machines (46)
COMP 520 Winter 2016 Virtual Machines (47)
COMP 520 Winter 2016 Virtual Machines (48)
COMP 520 Winter 2016 Virtual Machines (49)
Slides of this format from: http://cs.au.dk/~mis/dOvs/slides/39a-javavirtualmachine.pdf
COMP 520 Winter 2016 Virtual Machines (50)
COMP 520 Winter 2016 Virtual Machines (51)
COMP 520 Winter 2016 Virtual Machines (52)
COMP 520 Winter 2016 Virtual Machines (53)
COMP 520 Winter 2016 Virtual Machines (54)
COMP 520 Winter 2016 Virtual Machines (55)
COMP 520 Winter 2016 Virtual Machines (56)
COMP 520 Winter 2016 Virtual Machines (57)
COMP 520 Winter 2016 Virtual Machines (58)
COMP 520 Winter 2016 Virtual Machines (59)
COMP 520 Winter 2016 Virtual Machines (60)
COMP 520 Winter 2016 Virtual Machines (61)
COMP 520 Winter 2016 Virtual Machines (62)
COMP 520 Winter 2016 Virtual Machines (63)
COMP 520 Winter 2016 Virtual Machines (64)
COMP 520 Winter 2016 Virtual Machines (65)
COMP 520 Winter 2016 Virtual Machines (66)
COMP 520 Winter 2016 Virtual Machines (67)
COMP 520 Winter 2016 Virtual Machines (68)
COMP 520 Winter 2016 Virtual Machines (69)
COMP 520 Winter 2016 Virtual Machines (70)
COMP 520 Winter 2016 Virtual Machines (71)