1
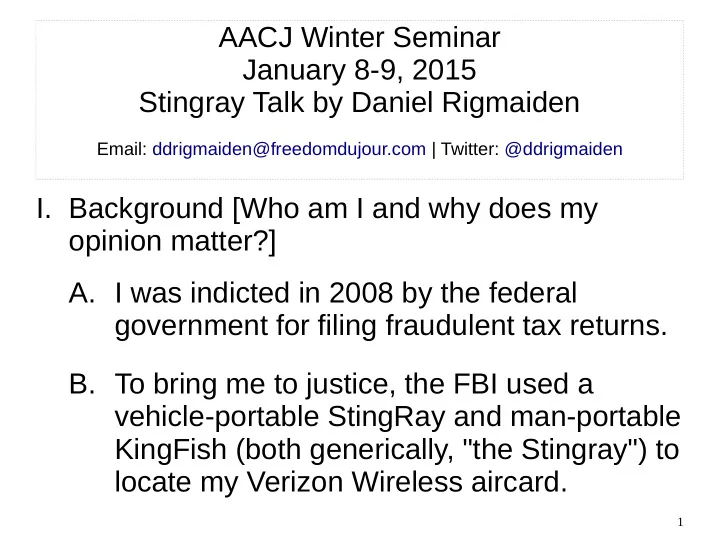
AACJ Winter Seminar January 8-9, 2015 Stingray Talk by Daniel Rigmaiden
Email: ddrigmaiden@freedomdujour.com | Twitter: @ddrigmaiden
- I. Background [Who am I and why does my
- pinion matter?]
- A. I was indicted in 2008 by the federal
government for filing fraudulent tax returns.
- B. To bring me to justice, the FBI used a