CPSC 418/MATH 318 Introduction to Cryptography
Number Theory, Security and Efficiency of Diffie-Hellman, Hash Functions Renate Scheidler
Department of Mathematics & Statistics Department of Computer Science University of Calgary
Week 6
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 6 1 / 28
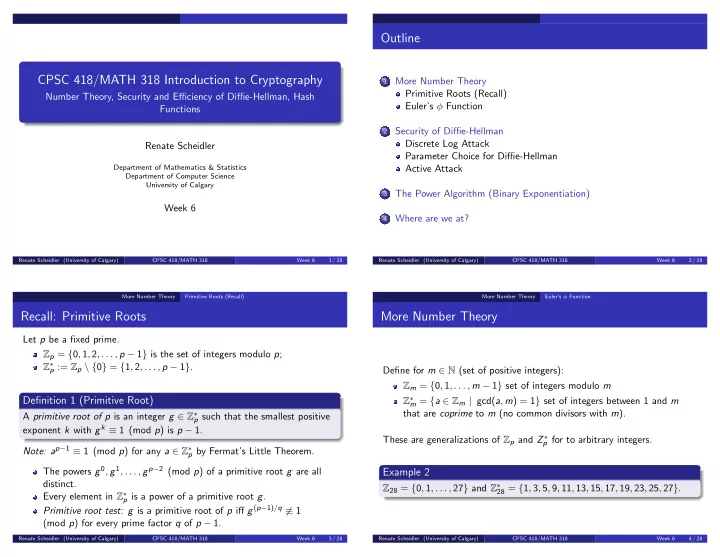
Outline
1
More Number Theory Primitive Roots (Recall) Euler’s φ Function
2
Security of Diffie-Hellman Discrete Log Attack Parameter Choice for Diffie-Hellman Active Attack
3
The Power Algorithm (Binary Exponentiation)
4
Where are we at?
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 6 2 / 28 More Number Theory Primitive Roots (Recall)
Recall: Primitive Roots
Let p be a fixed prime. Zp = {0, 1, 2, . . . , p − 1} is the set of integers modulo p; Z∗
p := Zp \ {0} = {1, 2, . . . , p − 1}.
Definition 1 (Primitive Root)
A primitive root of p is an integer g ∈ Z∗
p such that the smallest positive
exponent k with gk ≡ 1 (mod p) is p − 1. Note: ap−1 ≡ 1 (mod p) for any a ∈ Z∗
p by Fermat’s Little Theorem.
The powers g0, g1, . . . , gp−2 (mod p) of a primitive root g are all distinct. Every element in Z∗
p is a power of a primitive root g.
Primitive root test: g is a primitive root of p iff g(p−1)/q ≡ 1 (mod p) for every prime factor q of p − 1.
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 6 3 / 28 More Number Theory Euler’s φ Function
More Number Theory
Define for m ∈ N (set of positive integers): Zm = {0, 1, . . . , m − 1} set of integers modulo m Z∗
m = {a ∈ Zm | gcd(a, m) = 1} set of integers between 1 and m
that are coprime to m (no common divisors with m). These are generalizations of Zp and Z ∗
p for to arbitrary integers.
Example 2
Z28 = {0, 1, . . . , 27} and Z∗
28 = {1, 3, 5, 9, 11, 13, 15, 17, 19, 23, 25, 27}.
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 6 4 / 28