SLIDE 1
Risky Traitor Tracing and New Differential Privacy Negative Results - - PowerPoint PPT Presentation
Risky Traitor Tracing and New Differential Privacy Negative Results - - PowerPoint PPT Presentation
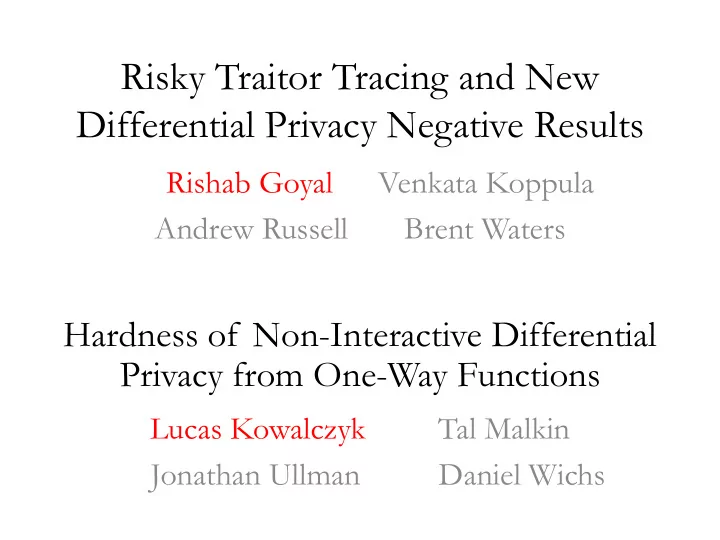
Risky Traitor Tracing and New Differential Privacy Negative Results Rishab Goyal Venkata Koppula Andrew Russell Brent Waters Hardness of Non-Interactive Differential Privacy from One-Way Functions Lucas Kowalczyk Tal Malkin Jonathan
SLIDE 2
SLIDE 3
Traitor Tracing [Chor-Fiat-Naor 94]
3
Key Challenges: (1) Obfuscated Decoder (2) Collusions
Decoder
Find Traitors
SLIDE 4
Tracing Algorithms
4
SLIDE 5
5
(1) No false trace: (2) Catch:
SLIDE 6
It’s About the Ciphertext Size!
PKE: Bilinear Maps [Boneh-Sahai-Waters06,Boneh-Waters06…]: Functional Encryption/iO[GGHRSW13,Boneh-Zhandry14]:
6
Can we get better efficiency from standard assumptions if we relax tracing requirement?
(* Subsequent to this work, G-Koppula-Waters gave an LWE-based standard TT scheme matching FE/iO-based efficiency.)
SLIDE 7
(1) No false trace: (2) Catch:
Relaxing Tracing
7
(1) No false trace: (2) Catch:
SLIDE 8
(Main) Results [G-Koppula-Russell-Waters]
SLIDE 9
Remaining Talk
Part I: Risky Traitor Tracing Part II: Differential Privacy Negative
9
Part II: Differential Privacy Negative Results (Luke)
SLIDE 10
- Persistent decoder setting
– Periodic key refreshes, decoder must work across cycles – Catching probability can be amplified
Standalone Risky TT Applications
- Resource constrained settings
– Get best possible tracing w/ 10 KB ciphertext overhead
- Risk averse attackers
– Deterrence against attackers if traitors heavily penalized – Heavy penalty vs. Low catching probability
SLIDE 11
Framework for Risky TT – Mixed Bit Matching Encryption
11
SLIDE 12
Mixed Bit Matching Security
Security: 3 properties PK/SK CT Hiding Distinguish
12
CT Hiding Key Hiding Distinguish Distinguish
SLIDE 13
Transformation to Risky TT
13
SLIDE 14
Transformation to Risky TT
14
SLIDE 15
Transformation to Risky TT
15
SLIDE 16
Transformation to Risky TT
Check if decoder is correct
16
is correct
Do this poly times
SLIDE 17
Transformation to Risky TT
Successful decryption probability
17
SLIDE 18
- Security proof of the transformation
– Significantly departs from existing proof techniques for TT
- Building Mixed Bit Matching Encryption from Bilinear
Missing Pieces and Other Results
- Building Mixed Bit Matching Encryption from Bilinear
Maps
- Generic risky amplification
– Improving success probability of tracing
18
SLIDE 19
Remaining Talk
Part I: Building Risky Traitor Tracing Part II: Differential Privacy Negative
19
Part II: Differential Privacy Negative Results (Luke)
SLIDE 20