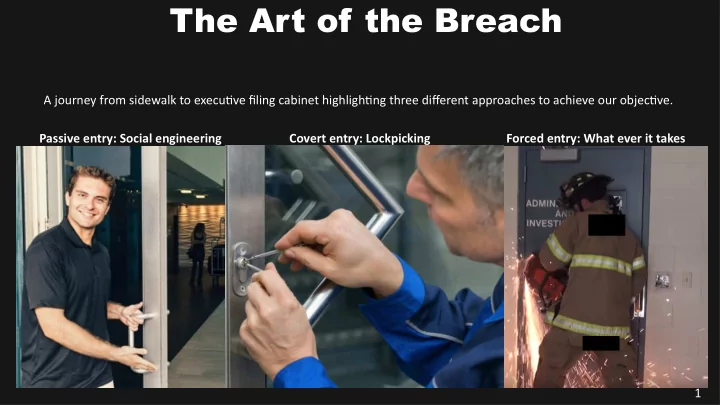
A journey from sidewalk to executjve fjling cabinet highlightjng three difgerent approaches to achieve our objectjve. Passive entry: Social engineering Covert entry: Lockpicking Forced entry: What ever it takes
The Art of the Breach
1
The Art of the Breach A journey from sidewalk to executjve fjling - - PowerPoint PPT Presentation
The Art of the Breach A journey from sidewalk to executjve fjling cabinet highlightjng three difgerent approaches to achieve our objectjve. Passive entry: Social engineering Covert entry: Lockpicking Forced entry: What ever it takes 1 The Art
A journey from sidewalk to executjve fjling cabinet highlightjng three difgerent approaches to achieve our objectjve. Passive entry: Social engineering Covert entry: Lockpicking Forced entry: What ever it takes
1
Founder: Nonprofjt Crowdsourced OSINT for Missing Persons www.tracelabs.org Profession: Senior IT Manager, Aerospace Industry www.linkedin.com/in/robertsell Volunteer: Coquitlam Search & Rescue: Tracker www.coquitlam-sar.bc.ca Twituer: @robertesell Email: robertesell@gmail.com
2
Housekeeping:
from past, present or future.
3
This content is being provided so that you may have a betuer understanding of criminal breach methodologies, allowing your
1 2 3 4 5 6 7 8 Research Target Prepare Pretexts Escape and Evade 3 4 5 6 7 Onsite Reconnaissance Front/Back Door Lobby Elevator/Stairs/Hallway Executjve Offjce
4
1
Passive reconnaissance / Zero touch recon:
5
1
Understand their business:
6
1
Understand their Infrastructure:
7
1
Understand their Defences:
8
2
Build pretexts on what was discovered in Stage 1:
9
2
Tips: Look like you belong. Look boring and predictably mundane (grey man). Backup pretexts if you get caught:
10
3
11
3
Look for:
12
4
Since our operatjon is lengthy and complex, a stealthy approach may be benefjcial where ever possible to avoid detectjon.
13
4
Passive Entry Method 1: Have Access Card
credentjal skimmer (ESP key) which is an interceptjon tool placed behind the card reader panel. Installatjon is a 5 minute job. 99% of these don’t have tamper alarms so low risk. Once installed, it collects creds and sends via wifj to your phone.
14
4
Passive Entry Method 2: Don’t have Access Card
15
4
Covert Entry Method
16
4
Forced Entry Method
17
4
Forced Entry Method: Key boxes
the building in proximity to the principal entrance.
possible exploit.
Success here gives you God Mode on the building.
18
19
20
place is a small set screw. Clam the jaw on, turn clockwise a quarter turn then counter clockwise untjl you completely spun out the cylinder. Once out, you can easily manipulate the locking mechanism with the modifjed handle.
21
tamper pin you may not be be able to defeat the latch with the shove knife.
a jamb (vertjcal support) which may need to be fjrst removed.
22
23
24
4
Passive Entry Method: Loading Dock
25
4
26
4
27
4
Covert/Forced Entry Method: Atuacking the Hinges
28
4
29
30
4
door with irons, cut the bolts, grind the bolt heads
4
Forced Entry Method: Atuacking Padlocks Ramset Cobra + Nail Gun: Used to take .22 calibre now takes .27 calibre rounds
31 No Country for Old Men
5
The lobby is a giant man trap as it likely has some
32
5
We want to either be:
past; or
avoid the lobby (alternate ingress point)
33
6
the atuacker.
either side.
movement.
34
6
35
6
36
7
37
7
Filing Cabinet - Passive entry:
Filing Cabinet - Covert entry:
Filing Cabinet - Forced entry:
38
8
39
You’re Probably Not Red Teaming... And Usually I’m Not, Either [SANS ICS 2018]: htups://www.youtube.com/watch?v=mj2iSdBw4-0 How to open a door without keys: htups://youtu.be/5mTYGfY0BhA Forcible Entry for Glass Commercial Doors: htups://youtu.be/MSQLDiboXCs Commercial Rear Door Forcible Entry: htups://youtu.be/7cEhNCjcxcg Halligan bar demonstratjon: htups://youtu.be/Pt7RPVoTd1E Firefjghter Forcible Entry: Pulling Hinges from a Metal Door and Jamb: htups://youtu.be/uOPw94LYsgM Inward Swinging Metal Door w/ Drop Bars - IRONS and LADDERS: htups://youtu.be/1yCT_eDn34c Door breaching: htups://en.wikipedia.org/wiki/Door_breaching Hardware Pentest Shop: htups://sneaktechnology.com/ How to Bypass RFID Badge Readers: htups://youtu.be/Ccm1caB6bao 8 Surprising Ways to Open Locks: htups://youtu.be/7Lsm4l3mRqw Cloning and Emulatjng RFID cards with Proxmark3: htups://youtu.be/W22juSqhJSA Dennis Maldonado - Real tjme RFID Cloning in the Field: htups://youtu.be/kUduHIygbY8 Elevator Hacking: From the Pit to the Penthouse: htups://youtu.be/ZUvGfuLlZus File Cabinet Lock Picked and Bypassed: htups://youtu.be/7R5VIz2U_MI Life Hack 2 - How to easily pick a fjling cabinet lock 2019: htups://youtu.be/AhAJN8wSALo Pick a Lock in SECONDS with a Bump Key: htups://youtu.be/WpH_t0u5Ybg RAMSET v MOUNTAIN Security DEADBOLT LOCK: htups://youtu.be/1oPRYz5D9jo STRONGER Ramset vs. Stronger Master Lock: htups://youtu.be/YREfmbQzVB4 The Pen-Sized Hinge Pin Destroyer: htups://youtu.be/nJu_-Iuppc0 Lock pick tools: htups://www.lockpicks.com/lock-entry-tools/lock-by-pass-tools.html
40
41